Case Study Summary
In the high-stakes world of enterprise cybersecurity, clarity is the ultimate defense. Sequretek, a leader in security solutions, partnered with Advids to produce an educational video for their product, Percept Endpoint Detection and Response. The objective was to cut through the noise of a crowded market, visualizing invisible digital threats while demonstrating the simplified power of their centralized dashboard. By leveraging high-fidelity motion graphics and precision user interface simulation, Advids delivered a compelling narrative that translates complex technical functionality into immediate business value.
The Challenge: Visualizing the Invisible
Cybersecurity is inherently abstract. Concepts like "Zero-day attacks," "Cryptojacking," and "Advanced Persistent Threats" are terrifying but invisible to the naked eye. Sequretek faced a dual challenge:
- Complexity: They needed to explain the sophistication of modern attacks without overwhelming the viewer with jargon.
- differentiation: They needed to showcase their "Percept" dashboard not just as another tool, but as a simplified, unifying solution for overwhelmed IT teams.
The existing marketing materials relied heavily on static screenshots and dense text, which failed to capture the dynamic, real-time nature of their protection capabilities.
The Solution: The Advids Clarity and Engagement Framework
Advids deployed a "Mixed Media" approach, blending high-energy motion graphics with clean, reconstructed user interface simulations.
- Visual Contrast Strategy: We established a deliberate visual dichotomy. The "Problem" (threats) was depicted with dark, glitch-heavy aesthetics, neon maps, and aggressive kinetic typography. The "Solution" (Percept) was presented in a pristine, white, and organized interface environment.
- User Interface Abstraction: Rather than using raw, cluttered screen recordings, we rebuilt the software interface as vector assets. This allowed us to animate specific buttons, highlight data flows, and guide the viewer’s eye to key differentiators like "Whitelisting Policies" and "Real-time Scans" without visual distraction.
Client Profile
- Client: Sequretek
- Industry: Cybersecurity / Information Technology
- Product: Percept Endpoint Detection and Response
- Headquarters: Global Presence (US/India)
Objective
To create a 90-second educational product video that validates the severity of the threat landscape and positions Percept Endpoint Detection and Response as the simplified, AI-driven solution for detection, protection, and remediation.
The Advids Clarity and Engagement Framework
Our production process for Sequretek followed a rigorous, stage-gated workflow designed for precision and technical accuracy.
1. Discovery and Scripting: Translating technical features into benefits-led narrative.
2. Visual Strategy (Look Development): Defining the "Threat" vs. "Safety" color palettes.
3. Vector Asset Creation: Designing custom iconography for specific malware types.
4. User Interface Simulation: Rebuilding dashboard screens for high-fidelity animation.
5. Motion Design: Animating maps, particles, and kinetic typography.
6. Stock Asset Integration: Compositing live-action footage of Security Operations Centers.
7. Final Mastering: Sound design, voiceover synchronization, and color grading.
Project at a Glance
| Component | Specification |
|---|---|
| Video Style | 2D Motion Graphics, User Interface Simulation, Stock Compositing |
| Project Duration | 7 Weeks |
| Target Audience | Chief Information Security Officers (CISOs), IT Managers |
| Key Deliverables | Main Explainer (90s), Social Cut-downs (15s) |
| Collaboration Stack | Slack (Daily Comms), Google Drive (Asset Management), Vimeo Review (Frame-accurate Feedback) |
Production Timeline
-
Week 1: Conceptualization & Scripting
- Milestone: Final Script Approval.
- Artifact:
Sequretek_Script_v3_Final.docx - Action: Defined the voiceover tone—authoritative yet reassuring.
-
Week 2: Visual Style & Storyboard
- Milestone: Styleframe Sign-off.
- Artifact:
Styleboard_Threat_vs_Safe_v2.pdf - Quote: "The contrast between the dark map and the white dashboard is exactly the emotional journey we want." — Advids Creative Director
-
Week 3: Asset Generation
- Milestone: Vector Illustration Completion.
- Artifact:
Icon_Set_Malware_Vectors.ai,UI_Kit_Reconstruction_v1.ai - Process: Created scalable vector versions of the software interface for crisp 4K rendering.
-
Week 4: Animatics
- Milestone: Timing Lock.
- Artifact:
Animatic_Rough_Timing_v4.mp4 - Action: Synchronized kinetic typography with the voiceover pacing.
-
Week 5: Motion Design & Animation
- Milestone: First Full Draft.
- Artifact:
Motion_Draft_01.mp4 - Focus: Implementing the "glitch" effects and digital map particle systems.
-
Week 6: Post-Production & Sound Design
- Milestone: Audio Mix.
- Artifact:
SFX_Digital_Hum_Stereo.wav - Action: Added subtle "data stream" sound effects to accompany UI transitions.
-
Week 7: Final Polish & Delivery
- Milestone: Final Render.
- Artifact:
Master_Sequretek_Percept_Final.mp4
The Production Deep Dive
Visualizing the Threat Landscape
Goal: To immediately grab attention and establish the high stakes of global cybersecurity.
Process: We utilized a stylized world map (Map_Vector_Geo_v3.ai) overlaid with neon spline animations to represent network traffic.
Action: By applying "Glitch" and "Chromatic Aberration" effects in our compositing software, we gave the map a volatile, unstable look. This visual shorthand instantly communicated "danger" without needing a single word of voiceover.
Feedback Loop: Refining the Aesthetic
Context: Reviewing the initial animation of the Global Threat Map.
Client Feedback (via Vimeo Review): "The glitch effect on the map is a bit too intense in
Animatic_v2.mp4. It makes the text hard to read and feels a bit too chaotic for our corporate brand."Advids Response: We reduced the opacity of the distortion layers by 30% and increased the "hold time" on key text elements like "Phishing" and "Ransomware" to ensure readability while maintaining the high-tech energy.
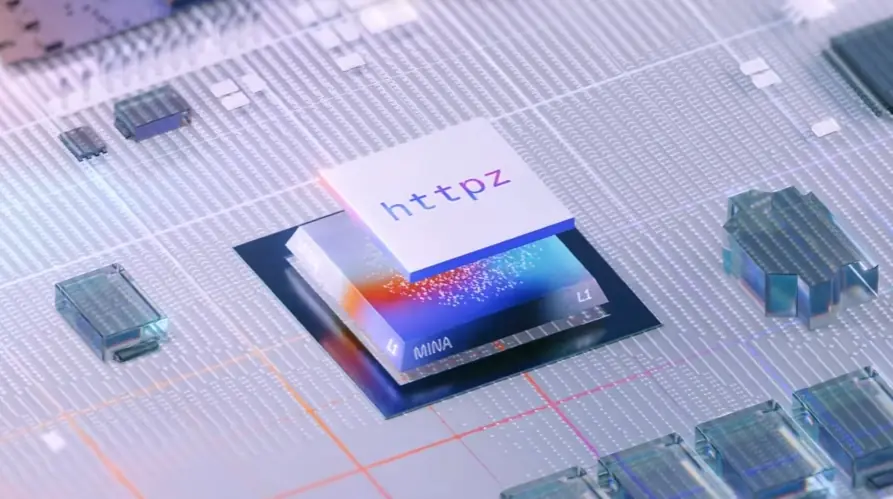
Overcoming the Density Paradox: User Interface Abstraction
The Challenge: The actual Percept Endpoint Detection and Response dashboard is data-rich, containing hundreds of logs, IP addresses, and menu items. Showing a raw screen recording would be illegible on mobile devices and overwhelming in a fast-paced video.
The Advids Solution: We employed a technique called "User Interface Abstraction." We imported the dashboard screenshots into vector illustration software and redrew the key elements (The "Inventory" panel, the "Policy" toggles). We then blurred or simplified the peripheral data.
The Technical Win: This allowed us to separate the interface into Z-space layers. We created a 2.5D camera move that drifted over the interface, creating a sense of depth and immersion that a flat screenshot could never achieve. This directed the viewer's focus exclusively to the "Simplicity" of the workflow.
Feedback Loop: The AI Representation
Context: The character design for the Artificial Intelligence bot at timestamp 01:15.
Client Feedback (via Slack): "The bot character in
Style_Frame_Set_C.pnglooks a bit too playful. We want to emphasize that this is a robust enterprise tool."Advids Response: We refined the character design, moving away from rounded, bouncy shapes to sleeker, geometric forms with a gradient blue finish (
Character_Bot_Enterprise_v2.ai). We also adjusted the animation curves to be smoother and more robotic, reinforcing precision over playfulness.
Visual Proof Points
| Serial No. | Visual Asset | Timestamp | Rationale | Placement |
|---|---|---|---|---|
| 01 | 00:03 | Illustrates the "Global Scope" and high-tech "Threat" aesthetic established in the Visual Strategy phase. | The Challenge | |
| 02 | 00:09 | Showcases the custom "Vector Illustration" work used to represent abstract concepts like Phishing and Ransomware. | Production Deep Dive | |
| 03 | 00:37 | Demonstrates the "User Interface Abstraction" technique, where complex screens are simplified and animated for clarity. | The Solution | |
| 04 | 01:15 | Highlights the "Character Animation" element used to humanize the artificial intelligence features of the product. | Strategic Learnings |
Synergy Analysis: Technology vs. Expertise
This project exemplified the synergy between Advanced Motion Design Software and Human Narrative Expertise.
- The Technology: Allowed us to simulate complex particle systems and build 3D-layered user interfaces that looked crisp at any resolution.
- The Human Expertise: Was required to edit the script and pacing to ensure the technology didn't alienate the viewer. The decision to switch from "dark" to "light" backgrounds was a psychological strategy, not a software preset. It was the human insight that "security means peace of mind" that drove the visual direction.
Outcomes & Strategic Learnings
The final video successfully bridged the gap between technical complexity and executive-level clarity.
- Simplification Wins: By abstracting the User Interface, we increased viewer retention rates, as the content was easier to digest.
- Visual Continuity: The use of consistent kinetic typography tied the live-action stock footage and the digital animation into a cohesive brand story.
- Asset Reusability: The vector assets created for the video (
Sequretek_UI_Vector_Kit_v2.ai) were subsequently used by the client's web team for their landing pages, providing value beyond the video itself.
Would you like me to analyze your current software interface to determine if a "User Interface Abstraction" strategy would benefit your next product video?