CASE STUDY: Cybersecurity Animation Video
Decoding Complexity for the Digital Consumer: A Motion Graphics Case Study##Executive SummaryIn the rapidly evolving landscape of digital payments, consumer trust is paramount. Our client, a global leader in payment technology, faced the challenge of communicating the intricate mechanics of "Visa Secure with EMV 3-D Secure." They required a video that could demystify complex fraud prevention protocols while assuring consumers of a frictionless online shopping experience. Advids leveraged the Advids Clarity & Engagement Framework to transform technical documentation into a fluid, accessible, and visually reassuring Two-Dimensional Motion Graphics narrative.
Decoding Complexity for the Digital ConsumerThe primary challenge was the "Transparency Paradox." The client needed to explain that their security protocol analyzes ten times more data than previous versions to prevent fraud, yet they needed to assure the user that this process would not slow down their shopping experience.
A literal visualization of data scanning often appears invasive or overly technical (resembling "The Matrix"), which could alienate the average online shopper. The objective was to visualize high-level security scrutiny as a seamless, background "invisible shield" rather than a hurdle. Furthermore, the visual language needed to balance the serious nature of cybersecurity with the bright, convenient lifestyle of the modern e-commerce consumer.
Visualizing the Invisible Shield via MotionAdvids proposed a strategic Two-Dimensional Motion Graphics approach, utilizing flat vector illustrations and kinetic typography to maintain clarity. Our solution focused on three core pillars:
- Metaphorical Simplification: We replaced lines of code with clean, orbiting iconography to represent data analysis.
- Fluid Transitions: We utilized continuous motion paths to signify the "frictionless" nature of the transaction process.
- Empathetic Character Design: We created relatable user avatars contrasted with stylized, non-terrifying threat representations to anchor the narrative in human experience.
By utilizing The Advids Clarity & Engagement Framework, we ensured that every frame served the dual purpose of technical education and brand reassurance.
Client Profile* Industry: Financial Technology / Payments
- Focus: Global secure payment protocols and consumer protection.
- Context: Introduction of the updated EMV 3-D Secure protocol for e-commerce.
Primary ObjectiveTo educate issuers, merchants, and consumers on how the new security protocol leverages contextual data to prevent fraud without adding friction to the checkout process.
The Advids Clarity & Engagement FrameworkFor this project, we deployed our specialized 2D animation workflow designed for high-stakes communication.
- Discovery & Scripting: Deconstructing technical whitepapers into a consumer-facing narrative.
- Visual Strategy: Defining the "Secure vs. Threat" visual language.
- Vector Illustration: creating scalable, brand-compliant assets.
- Animatics: Blocking out pacing and transition logic.
- Motion Design: Applying physics and easing for fluid movement.
- Sound Design: Creating an audio landscape that implies technology and safety.
Project at a Glance| Category | Details |
| --- | --- |
| Project Type | Cybersecurity Animation Video |
| Animation Style | Two-Dimensional Motion Graphics / Explainer |
| Core Technology | Adobe Creative Cloud (After Effects, Illustrator) |
| Deliverable Format | 1080p MP4 |
| Estimated Duration | 6 Weeks |
| Collaboration Stack | Slack (Real-time Communication), Google Drive (Asset Management), Vimeo Review (Video Feedback) |
Project Timeline* Week 1: Discovery and Scripting
-
Output:
Script_VisaSecure_V4.docx -
Milestone: Confirmed the "Data as a Shield" narrative angle.
-
Week 2: Visual Style Development
-
Output:
StyleFrame_Hacker_Concept_V2.ai,StyleFrame_DataOrbit_V1.ai -
Milestone: Approval of the character designs and color palette.
-
Week 3: Storyboarding and Animatics
-
Output:
Animatic_Flow_04.mp4 -
Quote: "The transition from the phone to the analysis cloud needs to feel instant. Let's speed up the pacing here." — Client Feedback via Vimeo Review
-
Week 4: Illustration and Asset Creation
-
Output:
Vector_Assets_Pack_Final.zip -
Milestone: Completion of all icon sets (Geolocation, Device ID, IP Address).
-
Week 5: Motion Design and Animation
-
Output:
Animation_Draft_01.mp4 -
Activity: Advids animators apply custom easing to particle flows.
-
Week 6: Sound Design and Final Mastering
-
Output:
N5A163_Final_Master.mp4 -
Milestone: Final delivery and file handoff.
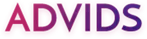
Orchestrating the Narrative: A Production Deep Dive###Phase 1: Conceptualizing the "Data Orbit"Goal: Visualize the analysis of "10 times more data" without creating visual chaos.
Process: The script called for a representation of contextual data sharing. Early iterations in Storyboard_Dataviz_V1.pdf used a linear pipeline metaphor, which felt too industrial and slow.
Critical Juncture: Advids pivoted to a radial design. We placed the word "Analyze" in the center of a golden circle, with key data points (represented by simple icons) orbiting it. This "Data Orbit" metaphor communicated comprehensive scanning occurring instantly, in 360 degrees.
Action: Our design team created StyleFrame_DataOrbit_V3.ai using a clean, concentric circle motif that aligned perfectly with the client's circular branding elements.
Phase 2: Balancing Threat and SafetyGoal: Depict the threat of fraud without scaring the consumer.
Process: The character design for the "Hacker" required nuance. In StyleFrame_Hacker_V1, the character was too dark and menacing, potentially distracting from the positive message.
Feedback Loop: Refining the Aesthetic:
Client: "The hacker figure feels a bit too cinematic villain. Can we make it more symbolic of a 'digital nuisance' rather than a physical threat?"
Advids: "Understood. We will lighten the background palette and use digital glitch effects to represent the threat, rather than shadowy lighting."
Action: We utilized Adobe Illustrator to flatten the character design and applied a "digital noise" effect in Adobe After Effects to depersonalize the threat, focusing on the action of hacking rather than the person.
Phase 3: Fluidity as a User Experience MetaphorGoal: Mirror the "frictionless" user experience through animation style.
Process: The protocol promises zero friction. Therefore, the animation could not have hard cuts or jerky movements.
Action: Advids utilized continuous motion paths. For example, the yellow circle from the "Visa Secure" logo morphs into the "Analyze" scanning tool, which then morphs into the "Biometric Approval" icon. This technique required complex Keyframe Animation and precise graph editor adjustments to ensure momentum was preserved across scenes.
Visual Asset Highlights| Serial No. | Visual Asset | Timestamp | Rationale | Placement |
| --- | --- | --- | --- | --- |
| 1 | The Digital Threat | 00:14 | Illustrates the stylized, non-threatening depiction of the "Hacker" utilizing digital glitch effects. | Design Strategy |
| 2 | The Data Orbit | 00:36 | The "Critical Juncture" solution: visualizing massive data intake via clean, radial iconography. | Production Deep Dive |
| 3 | False Positive Context | 01:04 | Visualizes specific use-cases (travel) where data context prevents legitimate declines. | Narrative Structure |
| 4 | Biometric Resolution | 01:31 | The climax of the User Experience, showing the "frictionless" approval via fingerprint. | Conclusion |
Synergy Analysis: Technology meets IntuitionThis project exemplifies the synergy between advanced animation software and strategic storytelling. While Adobe After Effects provided the technical capability to create complex particle systems and morphing shapes, it was the Advids creative strategy that determined why those shapes should morph. We used technology not just to make things move, but to translate the abstract code of EMV 3-D Secure into the tangible feeling of safety.
Outcomes and Strategic LearningsThe final video successfully demystified the backend security process for the client's audience.
- Clarity: The "Data Orbit" visualization became a key asset for the client in explaining the "Contextual Data" concept.
- Brand Alignment: The video maintained 100% adherence to the client's visual identity, reinforcing brand trust.
- Strategic Learning: We reinforced that in cybersecurity communication, "less is more." By abstracting complex data into clean icons, we communicated sophistication and speed more effectively than detailed technical diagrams ever could.
Would you like me to develop a complementary social media teaser strategy derived from this main case study?