Introduction: Visualizing the Invisible Shield
In the high-stakes arena of SaaS security, the "Castle and Moat" era is over. Today’s perimeter is everywhere—it is the user’s device, their biometric signature, and their behavior. For CISOs and Product Leaders, the challenge is no longer just building a robust Multi-Factor Authentication (MFA) engine; it is about communicating that robustness without triggering "security fatigue." We are designing for a Zero Trust world where the goal is to make the lock invisible until the moment it is needed.
The market demand for this sophisticated, frictionless security is exploding. The global multifactor authentication sector is projected to reach USD 45.30 billion by 2030, driven by a massive shift toward cloud-native identity solutions. However, the operational reality is often messy. Adoption lags not because the technology fails, but because the experience creates friction. Yet, the cost of inaction is staggering; with the global average cost of a data breach reaching USD 4.88 million in 2024, the imperative to bridge the gap between security and usability is existential.
This guide serves as your visual blueprint for bridging that "Physical/Digital Divide." It curates 30 distinct visual styles designed to translate abstract cryptographic concepts—like FIDO2 handshakes and adaptive risk scoring—into tangible, confidence-inspiring assets. By applying these styles, you do more than demonstrate features; you visually engineer trust, proving to your stakeholders that your platform is as usable as it is unbreakable.
1. The Liquid Data Shield
TOFU | Brand Awareness
The Visual & Narrative Approach
Visualization Scenario: Security is often perceived as rigid and blocking. This style reframes it as fluid and adaptive. The visual features scattered droplets of vivid sky blue and soft white "liquid data" drifting in an abstract grey space. As a threat (or user request) approaches, these droplets intelligently coalesce, forming a glossy shield around a central mint-green core.
Narration Style: Smooth, reassuring, and sophisticated. "Protection that adapts to you, not the other way around."
Psychological Impact & KPI Focus
- Niche Psychology: Addresses the "Fear of Friction." By using organic, liquid motion, we subconsciously signal that the software is flexible and integrates smoothly into existing workflows, rather than being a clunky bolt-on.
- Operational Impact: Visualizes Adaptive Risk Assessment. It shows protection forming only when necessary, reducing the perceived cognitive load on the end-user.
Strategic Implementation & Trade-offs
- Best Use: Website Hero Video (Looping).
- Duration: 10-15 Seconds.
- Trade-off: Abstract vs. Technical. Excellent for establishing a modern brand "vibe," but fails to explain how the encryption actually works.
Companies using similar video content -
SecureAuth – Adaptive Authentication – Fluidly adapts security to user risk.
Silverfort – Identity Protection Platform – Intelligently coalesces defense against threats.
2. The Blueprint to Reality
TOFU | Market Education
The Visual & Narrative Approach
Visualization Scenario: A split-screen composition that reads left-to-right. The left side reveals the "bones" of the software—a technical blue wireframe blueprint of a padlock. As the eye scans right, this wireframe instantly transforms into a photorealistic, heavy-duty brushed silver mechanism with safety orange accents. The lighting shifts from digital schematic to high-contrast realism.
Narration Style: Authoritative and engineering-focused. "Built on precision code. Forged into ironclad reality."
Psychological Impact & KPI Focus
- Niche Psychology: IT decision-makers are skeptical of "vaporware." They respect engineering. This style triggers the "Build Quality" Heuristic, validating the product by showing the underlying architecture before the final polish.
- Operational Impact: Bridges the Physical/Digital Divide. It gives "weight" to the software, implying that the digital gateway is as robust as a physical vault door.
Strategic Implementation & Trade-offs
- Best Use: YouTube "How it Works" Intro.
- Duration: 15-20 Seconds.
- Trade-off: Industrial Aesthetic. The heavy mechanical look implies "Infrastructure Security" rather than "Consumer Ease." Use carefully if targeting non-technical users.
Companies using similar video content -
Thales – CipherTrust Data Security Platform – Engineered trust for data security.
Entrust – Identity as a Service – Blueprinting robust digital identity solutions.
3. The Biometric Morph
TOFU | Shaping Brand Perception

The Visual & Narrative Approach
Visualization Scenario: A minimalist 1:1 canvas in solid cream. A geometric key icon (representing legacy passwords) in matte coral sits centrally. In a smooth, elastic animation, the key melts and reforms into a clean biometric fingerprint pattern in slate grey. No clutter, no complex backgrounds—just the evolution of access.
Narration Style: Minimal. "From what you carry... to who you are."
Psychological Impact & KPI Focus
- Niche Psychology: "Cognitive Ease" is the priority here. The simple morphing animation reassures the viewer that upgrading to passwordless MFA is a natural, painless step, not a complex migration.
- Operational Impact: Visualizes Modernization. It creates a clear "Old Way vs. New Way" dichotomy without using negative imagery, driving positive brand sentiment on social channels.
Strategic Implementation & Trade-offs
- Best Use: LinkedIn/Instagram Carousel Slide.
- Duration: 6-10 Seconds (Looping).
- Trade-off: Oversimplification. It does not convey the security depth (e.g., FIDO2 standards), only the concept of the upgrade.
Companies using similar video content -
HYPR – True Passwordless Security – Seamlessly morphs to biometric access.
Keyless – Biometric Authentication – Evolves access from keys to biometrics.
4. The Glass Box Architecture
TOFU | Risk Mitigation
The Visual & Narrative Approach
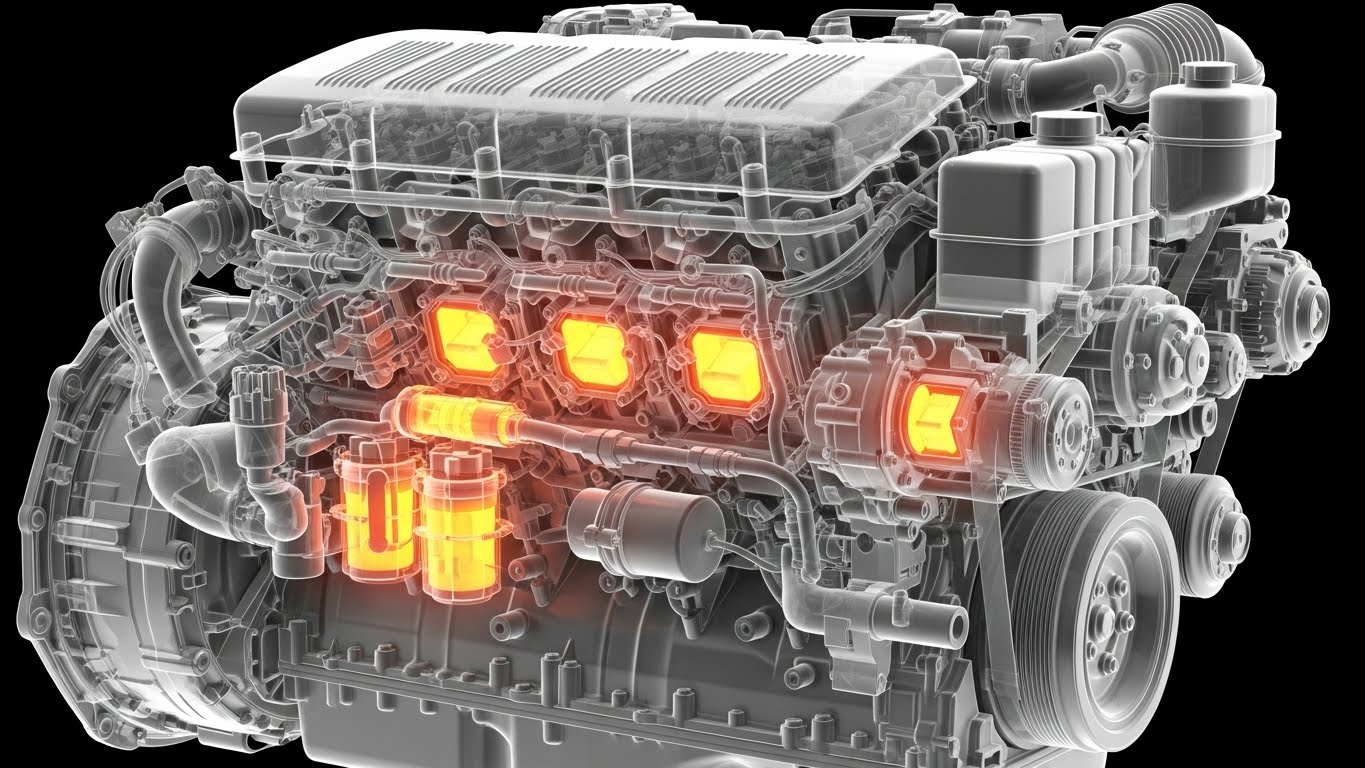
Visualization Scenario: To build deep trust, we must look inside. An isometric view of a server rack is rendered in translucent cyan glass. This X-Ray view reveals the active components: glowing neon green encryption keys and firewall barriers that physically block red threat data. The clinical white environment suggests a sterile, controlled laboratory.
Narration Style: Analytical. "We don't ask for blind trust. We offer total transparency."
Psychological Impact & KPI Focus
- Niche Psychology: Security architects fear the "Black Box." This style uses transparency to mitigate risk perception. If they can see the internal mechanism, they feel more in control.
- Operational Impact: Visualizes Defense in Depth. It proves that security is layered (hardware + software), supporting the technical validation phase of the buying cycle.
Strategic Implementation & Trade-offs
- Best Use: Product Page "Architecture" Section.
- Duration: 20-30 Seconds.
- Trade-off: Complexity. Can be visually overwhelming for C-suite executives who only care about the bottom line. Keep it for technical audiences.
Companies using similar video content -
CyberArk – Identity Security Platform – Reveals layered internal security architecture.
BeyondTrust – Privileged Access Management – Transparently controls internal access.
5. The Friction Contrast
TOFU | LinkedIn Organic

The Visual & Narrative Approach
Visualization Scenario: A vertical split-screen designed to stop the scroll. The top half is dark and chaotic: a stressed worker fumbling with sticky notes. The bottom half is bright and aspirational: a professional seamlessly logging in with a teal biometric scan on their phone. The contrast highlights the emotional difference between legacy security and your platform.
Narration Style: Empathetic. "Top: The cost of 'secure enough.' Bottom: The ROI of frictionless trust."
Psychological Impact & KPI Focus
- Niche Psychology: Leverages Empathy. It acknowledges the pain of password fatigue and offers an immediate visual solution. It humanizes the B2B buyer's problem (employee complaints).
- Operational Impact: Visualizes Productivity Gains. It frames the security purchase as a productivity tool, not just a compliance cost.
Strategic Implementation & Trade-offs
- Best Use: LinkedIn Organic Video / Shorts.
- Duration: 15-20 Seconds.
- Trade-off: Production Value. Requires high-quality acting to avoid looking like a cheesy infomercial. The "Teal Overlay" must look integrated, not pasted on.
Companies using similar video content -
Okta – Workforce Identity Cloud – Contrasts friction with seamless user flow.
Duo Security (Cisco) – Trusted Access – Highlights ROI of frictionless security.
6. Kinetic Integration
TOFU | Vertical Social Organic

The Visual & Narrative Approach
Visualization Scenario: Pure energy. Blocky, geometric shapes in electric indigo and hot pink pulse and expand. They slam together, interlocking like a complex puzzle or a bank vault mechanism. The motion blur and camera shake emphasize the speed and solidity of the connection.
Narration Style: Upbeat, rhythmic. "Snap. Lock. Done."
Psychological Impact & KPI Focus
- Niche Psychology: Appeals to the "Speed" heuristic. Modern dev teams want tools that "snap" into their stack (API-first). This visualizes that seamless, forceful integration.
- Operational Impact: Visualizes API Connectivity. The interlocking shapes suggest compatibility and structural integrity without needing a flow chart.
Strategic Implementation & Trade-offs
- Best Use: TikTok/Reels Hype Video.
- Duration: 5-10 Seconds.
- Trade-off: Zero Information. It is a "vibe" video. It must be accompanied by a caption explaining what is integrating.
Companies using similar video content -
Stytch – Authentication Platform – Kinetic integration for developer-first auth.
Descope – AuthN Platform – Snaps together authentication flows instantly.
7. The Digital Iris
TOFU | Skippable Pre-Roll Ad
The Visual & Narrative Approach
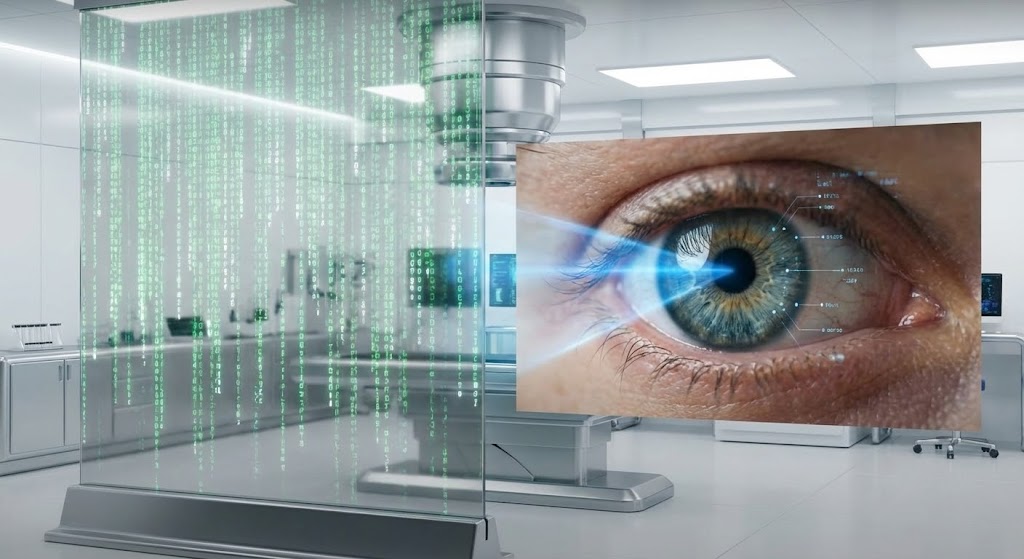
Visualization Scenario: A bridge between worlds. We start with "digital rain" (Matrix code) in clean green. As the camera zooms, the code morphs into the texture of a human iris. We pull back to see a cinematic shot of a human eye being scanned in a futuristic white lab. This transition visually argues that the human body is the ultimate code.
Narration Style: Visionary. "Your unique code isn't written on a server. It's written in you."
Psychological Impact & KPI Focus
- Niche Psychology: Taps into the Futurism trend. It positions the brand as an innovator using AI and biometrics, distancing it from legacy "password" vendors.
- Operational Impact: Visualizes Inherence Factors. It creates a strong association between the platform and advanced biometric capability.
Strategic Implementation & Trade-offs
- Best Use: YouTube Pre-Roll Ad (First 5 seconds hook).
- Duration: 15-30 Seconds.
- Trade-off: Uncanny Valley. The transition from code to eye must be high-fidelity. If the eye looks fake, trust is lost immediately.
Companies using similar video content -
ID.me – Digital Identity Network – Transforms digital code into human identity.
Jumio – Identity Verification – AI-generated digital identity from human features.
8. The Neural Brain
MOFU | Establishing Thought Leadership
The Visual & Narrative Approach
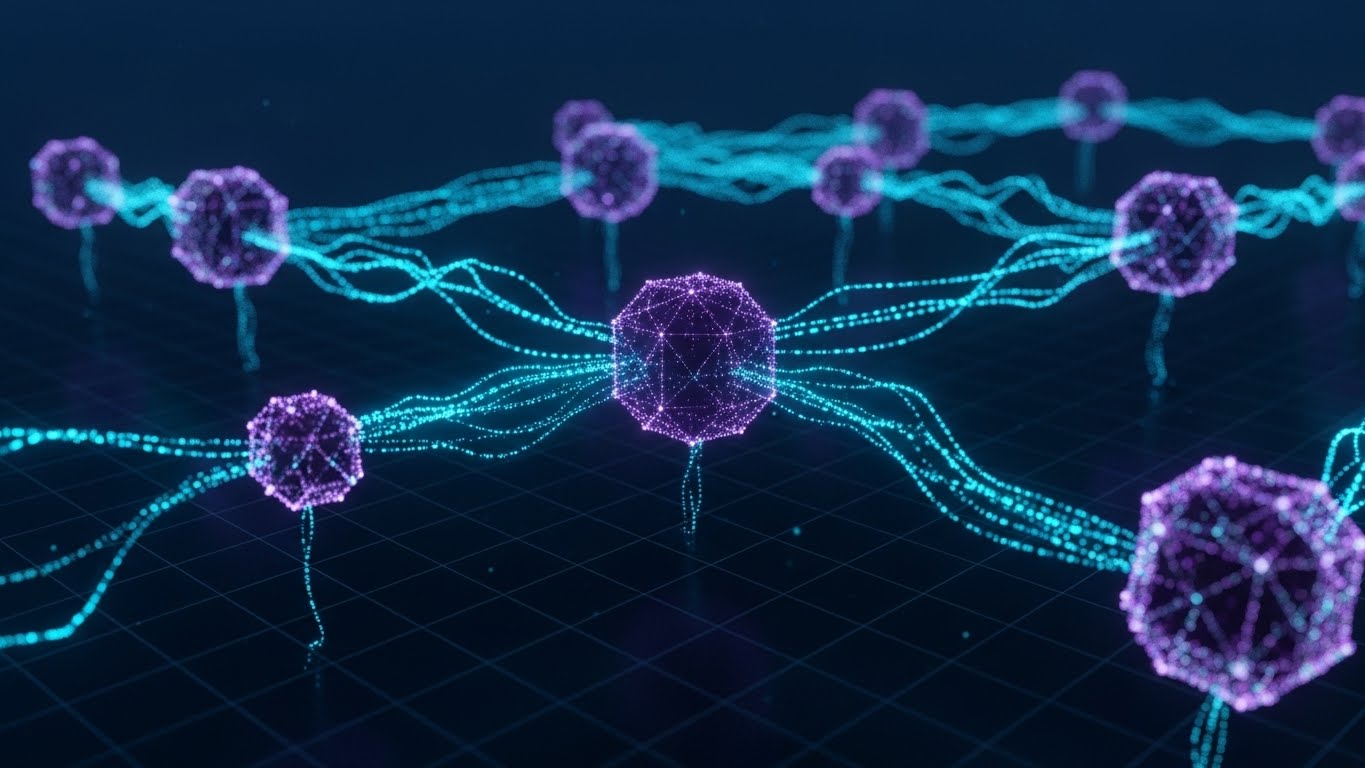
Visualization Scenario: To explain "AI-Driven Risk Analysis," we visualize a brain. Deep purple nodes float in a void, connected by pulsating filaments. When a threat appears (red pulse), the network actively re-routes connections to bypass it. The camera floats through this infinite digital space, observing the system's autonomy.
Narration Style: Intellectual and data-driven. "Security that thinks. Adapting faster than any threat."
Psychological Impact & KPI Focus
- Niche Psychology: Buyers want "Smart" tools. This visual proves the system is proactive, not reactive. It justifies the premium price of AI-based security.
- Operational Impact: Visualizes Invisible Backend Processes. It gives form to the algorithms that run in the background, making the AI tangible.
Strategic Implementation & Trade-offs
- Best Use: Blog Post Header / Whitepaper Background.
- Duration: 20-30 Seconds (Looping).
- Trade-off: Abstract. It explains the concept of AI, but not the specific rules. Best used to set the tone for a technical deep dive.
Companies using similar video content -
Authsignal – Fraud Operations Platform – Visualizes AI-driven risk analysis.
Silverfort – Identity Protection Platform – Neural network for intelligent threat routing.
9. The Verification Factory
MOFU | Product/Solution Differentiation

The Visual & Narrative Approach
Visualization Scenario: An isometric view of an infinite grid. Pastel blue and yellow tokens (users) glide along conveyor belts. They pass through white verification gates. Valid tokens turn green and continue; invalid ones turn red and drop off. The motion is clockwork—rhythmic, organized, and efficient.
Narration Style: Instructional. "Process millions without a pause. The verification engine never blinks."
Psychological Impact & KPI Focus
- Niche Psychology: Operations managers value Order and Scale. This style reassures them that the MFA implementation won't become a bottleneck during traffic spikes.
- Operational Impact: Visualizes Traffic Shaping & Latency. It transforms the abstract concept of "requests per second" into a visual manufacturing process.
Strategic Implementation & Trade-offs
- Best Use: Website "Features" Section.
- Duration: 30-45 Seconds.
- Trade-off: Simplicity. Great for showing flow, but doesn't show the security depth. It assumes the gates work; it doesn't show how.
Companies using similar video content -
Prove – Identity Verification – Processes millions of verifications efficiently.
Transmit Security – Identity Experience Platform – Orchestrates scalable verification flows.
10. The Tactile Toggle
MOFU | Feature Education & Demonstration

The Visual & Narrative Approach
Visualization Scenario: A macro close-up of the UI. A toggle switch slides from grey to lime green. As it clicks, a subtle protective ripple emanates from the switch, distorting the air slightly. The focus is razor-sharp on the texture of the button.
Narration Style: Focused. "One click. Total lockdown."
Psychological Impact & KPI Focus
- Niche Psychology: The Completion Principle. The satisfying "click" and visual ripple provide positive reinforcement, making the act of securing the system feel empowering rather than tedious.
- Operational Impact: Visualizes Ease of Administration. It counters the fear of complex configuration dashboards.
Strategic Implementation & Trade-offs
- Best Use: Email Newsletter GIF / Feature Update.
- Duration: 3-5 Seconds.
- Trade-off: Context. It shows the trigger, not the effect. Use it to highlight usability updates, not architectural changes.
Companies using similar video content -
Microsoft Azure AD – Identity & Access Management – Instant activation with a tactile toggle.
Google Cloud Identity – Identity and Access Management – One-click security activation.
11. The Clarifying Line
MOFU | Overcoming Objections
The Visual & Narrative Approach
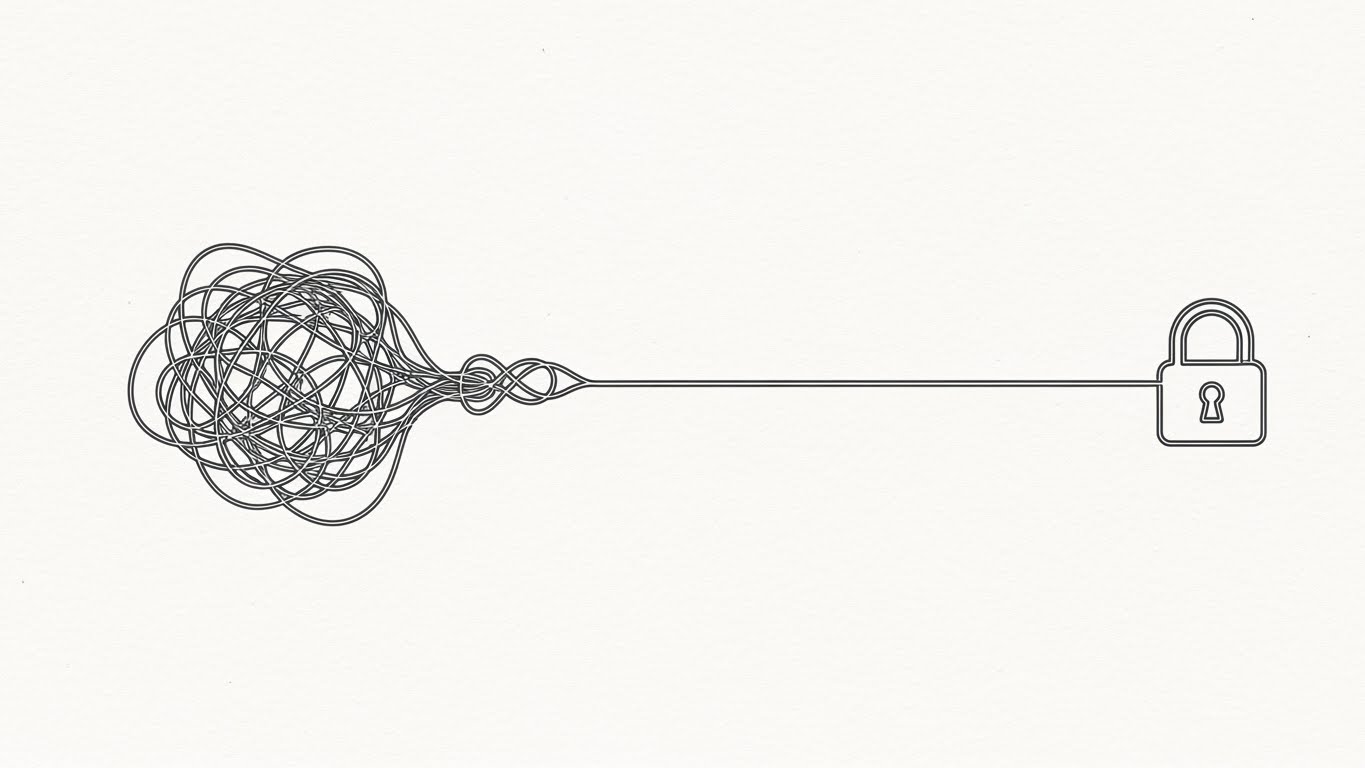
Visualization Scenario: Addressing "Implementation Paralysis" requires radical simplicity. We utilize a continuous 2D line art animation in charcoal grey against a tactile, chalk-white paper-textured background. On the left, a chaotic, tangled knot of lines represents the prospect's current fragmented security stack. In a sophisticated, fluid motion, this knot smoothly unravels and straightens into a single, elegant horizontal line that leads directly to a simple, sturdy lock icon.
Narration Style: Calming and solution-oriented. "Complexity is the enemy of security. We simply straighten the line."
Psychological Impact & KPI Focus
- Niche Psychology: Touches on the Cognitive Load of IT administrators. The visual metaphor of "unravelling the knot" promises a reduction in mental effort and technical debt.
- Operational Impact: Visualizes Workflow Consolidation. It demonstrates how the platform unifies disparate protocols (SAML, OIDC) into a single, linear management stream.
Strategic Implementation & Trade-offs
- Best Use: Sales Deck "Solution" Slide / One-Pager Header.
- Duration: 5-8 Seconds (Looping).
- Trade-off: Minimalism. It is purely metaphorical. It works best when paired with hard data or a case study to ground the promise in reality.
Companies using similar video content -
Strata Identity – Identity Orchestration Platform – Untangles complex identity paths.
WSO2 Identity Server – Open Source IAM – Simplifies integration with clarifying lines.
12. The Titanium Token
MOFU | Competitive Displacement

The Visual & Narrative Approach
Visualization Scenario: To displace cheaper, software-only competitors, we visualize the weight of protection. A photorealistic 3D render focuses on a futuristic hardware authentication token, finished in heavy brushed titanium. A glowing LED blue ring pulses slowly on its surface. The object floats in a premium studio environment with softbox lighting that catches sharp, metallic reflections. The low-angle camera shot emphasizes its build quality and impenetrable nature.
Narration Style: Premium and robust. "Not just a code. A key. Forged for the enterprise."
Psychological Impact & KPI Focus
- Niche Psychology: Triggers the "Tangibility Bias." Even if the solution is SaaS, associating it with a high-fidelity physical object makes the value feel more substantial and "expensive" (in a good way).
- Operational Impact: Visualizes Hardware-Backed Security. It reassures buyers that the platform supports the highest assurance levels (FIDO2/AAL3).
Strategic Implementation & Trade-offs
- Best Use: Landing Page Hero / Feature Spotlight.
- Duration: 10-15 Seconds.
- Trade-off: Hardware Focus. If your solution is 100% passwordless/biometric and doesn't use tokens, this style might be misleading. Ensure it matches your support matrix.
Companies using similar video content -
Yubico – YubiKey – Photorealistic render of a premium hardware token.
Feitian – FIDO Security Keys – Tangible token for premium assurance.
13. The Enterprise Fortress
MOFU | ABM Awareness

The Visual & Narrative Approach
Visualization Scenario: Targeting the Enterprise segment requires showing the solution in the real world. We use high-quality footage of a modern glass corporate office building exterior. Overlaying this reality are stylized 2D vector shield icons in "Corporate Blue," floating protectively around the structure's perimeter. These graphic elements are semi-transparent, blending seamlessly with the architectural perspective to suggest a digital layer protecting physical assets.
Narration Style: Grand and corporate. "Protecting the headquarters. And the workforce within."
Psychological Impact & KPI Focus
- Niche Psychology: Appeals to the "Duty of Care" felt by enterprise CISOs. Seeing the physical building protected by the software reinforces the gravity of their responsibility.
- Operational Impact: Visualizes Perimeter Security. It translates the abstract concept of a firewall or geofencing into a literal shield around the corporate footprint.
Strategic Implementation & Trade-offs
- Best Use: LinkedIn Ads targeting specific accounts (ABM).
- Duration: 15-20 Seconds.
- Trade-off: Generic Corporate Imagery. Can feel like stock footage if the graphics aren't high-quality. The motion tracking of the shields must be perfect to maintain immersion.
Companies using similar video content -
Palo Alto Networks – Prisma Access – Shields corporate buildings with digital defense.
Fortinet – FortiGate – Protects enterprise perimeters with a corporate shield.
14. The Admin Zen
MOFU | The Functional Buyer
The Visual & Narrative Approach
Visualization Scenario: The admin is the gatekeeper. We show them a world of order. A simplified admin dashboard screen is displayed in surgical white and light grey. The layout is card-based and spacious, featuring abstract representations of user activity graphs and "Active" status indicators in soft green. There is no readable text—just abstract lines and shapes representing data flow, emphasizing the feeling of control rather than specific metrics.
Narration Style: Efficient. "Complexity, managed. Insight, delivered."
Psychological Impact & KPI Focus
- Niche Psychology: Admin panels are notoriously cluttered. This "Zen" aesthetic promises Operational Efficiency, appealing to the functional buyer who fears spending their day fighting fires.
- Operational Impact: Visualizes Ease of Administration. It highlights the "Single Pane of Glass" visibility, a critical requirement for SOC teams managing thousands of identities.
Strategic Implementation & Trade-offs
- Best Use: Whitepaper Interstitial / Product Page "Ease of Use" Section.
- Duration: 10-15 Seconds.
- Trade-off: Lack of Detail. It sells the experience of the UI, not the specific features. Not suitable for technical documentation or "How-to" guides.
Companies using similar video content -
JumpCloud – Cloud Directory Platform – Minimalist dashboard for operational clarity.
OneLogin (One Identity) – Trusted Experience Platform – Clean UI for admin zen.
15. The Developer's Canvas
MOFU | The Technical Buyer

The Visual & Narrative Approach
Visualization Scenario: Developers don't trust marketing; they trust code. We present a computer terminal screen in deep obsidian. Cascading lines of code (SDK integration scripts) scroll in neon cyan and green. The perspective is slightly tilted, and subtle reflections of a dark server room are visible on the screen surface. The aesthetic is unapologetically technical, high-contrast, and focused on the "build."
Narration Style: Technical and direct. "Three lines of code. Enterprise-grade security. Push to commit."
Psychological Impact & KPI Focus
- Niche Psychology: Validates the "Developer Experience" (DX). It signals that the platform is API-first and developer-friendly, not a bloated legacy software that will delay their sprint.
- Operational Impact: Visualizes Rapid Integration. It serves as visual proof of the "Low Code / No Code" or "SDK simplicity" claims made in your sales collateral.
Strategic Implementation & Trade-offs
- Best Use: Technical Specs Page / Developer Documentation Header.
- Duration: 6-10 Seconds (Looping).
- Trade-off: Alienating Non-Techs. This style is dark and code-heavy. It may look intimidating to a non-technical CEO. Use strictly for technical stakeholders.
Companies using similar video content -
Auth0 (Okta) – Identity Platform – Showcases neon code for developer credibility.
Stytch – Authentication Platform – Dark mode UI for rapid integration.
16. The Modular Blockade
BOFU | Demand Gen & Lead Capture

The Visual & Narrative Approach
Visualization Scenario: Security is a sum of parts. We use abstract 2D motion graphics featuring geometric primitives. Triangles in vibrant orange and circles in geometric blue spin and lock together with mechanical precision to form a solid, impenetrable wall pattern. The background features a subtle tessellated pattern. The motion is snappy, rhythmic, and conveys the strength of a perfectly assembled system.
Narration Style: Rhythmic. "Build your wall. Brick by verified brick."
Psychological Impact & KPI Focus
- Niche Psychology: Appeals to the "Gestalt Principle"—the whole is greater than the sum of its parts. It reassures buyers that your specific tool fits perfectly into their existing security stack (firewalls, IAM, SIEM).
- Operational Impact: Visualizes Interoperability. It symbolically demonstrates how the MFA engine integrates with existing infrastructure to create a unified defense posture.
Strategic Implementation & Trade-offs
- Best Use: Display Ads (Google Display Network) / Retargeting Banners.
- Duration: 3-5 Seconds (Looping GIF).
- Trade-off: Abstract. It creates a strong "feeling" of security but conveys zero information about the product itself. Strictly a brand reinforcement tool.
Companies using similar video content -
SailPoint – Identity Platform – Builds a modular blockade with geometric precision.
Saviynt – Enterprise Identity Cloud – Integrates security components into a solid wall.
17. The Executive Confidence
BOFU | Building Trust & Credibility

The Visual & Narrative Approach
Visualization Scenario: Ultimately, security is about people. We feature a realistic character video of a professional CISO standing in a modern executive boardroom with glass walls. She holds a tablet, looking at it with a confident, relaxed expression as a soft teal light from the screen illuminates her face. The lighting is cinematic and warm, contrasting with the cold "hacker" stereotypes often used in the industry.
Narration Style: Human and assuring. "Sleep soundly. We’re watching the gate."
Psychological Impact & KPI Focus
- Niche Psychology: Uses Social Proof and mirroring. The viewer (likely a security leader) sees themselves in the calm, confident figure. It validates their aspiration to be in control, rather than in crisis mode.
- Operational Impact: Visualizes Governance & Compliance. It moves the conversation from "blocking attacks" to "managing risk," which is the language of the boardroom.
Strategic Implementation & Trade-offs
- Best Use: Case Study Header / Testimonial Video B-Roll.
- Duration: 5-10 Seconds.
- Trade-off: Casting Authenticity. If the AI generation looks "uncanny," it backfires. The expression must be perfectly nuanced—confident, not smug.
Companies using similar video content -
Simeio Solutions – Managed Identity Services – Projects executive confidence in security posture.
Omada – Identity Governance & Administration – Reassures executives with confident leadership.
18. The Growth Guardian
BOFU | ROI Justification

The Visual & Narrative Approach
Visualization Scenario: Security is an investment, not a cost. In a clean white studio void, we see 3D bar charts in "Data Blue" and "Growth Green" rising rapidly like skyscrapers. As they ascend, a translucent, glass-like dome forms protectively over the charts. The camera angle is high, looking down at this growing "data city," emphasizing that the growth is contained and safe.
Narration Style: Business-focused. "Secure your upside. Protect your growth."
Psychological Impact & KPI Focus
- Niche Psychology: Addresses Loss Aversion. It frames security not as a cost center, but as an insurance policy for revenue. It connects the software directly to the company's financial success.
- Operational Impact: Visualizes Business Continuity. It implies that with proper MFA, downtime is eliminated, allowing business metrics (the charts) to grow unimpeded by breaches.
Strategic Implementation & Trade-offs
- Best Use: Investor Presentation / CFO Pitch Deck.
- Duration: 8-12 Seconds.
- Trade-off: Corporate Vibe. It is very formal. It works for the CFO, but might bore the hacker/security engineer. Tailor the audience accordingly.
Companies using similar video content -
Zscaler – Zero Trust Exchange – Protects business growth with a security dome.
CrowdStrike – Falcon Platform – Guards enterprise growth with dynamic data visualization.
19. The Anywhere Access
BOFU | Driving Demo Requests

The Visual & Narrative Approach
Visualization Scenario: The perimeter is now the coffee shop. We use a lifestyle photo of a young professional working on a laptop in a warm, sunlit cafe. Overlaid on the laptop screen is a crisp, digital blue UI element showing a checkmark and a progress bar completing instantly. The shot is over-the-shoulder, focusing on the screen interaction while maintaining the cozy, friction-free atmosphere of the environment.
Narration Style: Liberating. "Work anywhere. Secure everywhere."
Psychological Impact & KPI Focus
- Niche Psychology: Validates the "Work from Anywhere" lifestyle. It assures the user that high security doesn't mean being chained to a VPN or a physical office.
- Operational Impact: Visualizes Context-Aware Access. It implies the system is smart enough to verify users in untrusted environments (public Wi-Fi) without blocking them.
Strategic Implementation & Trade-offs
- Best Use: Email Signature Banner / "Book a Demo" Page.
- Duration: Static Image or subtle Cinemagraph.
- Trade-off: Consumer vs. Enterprise. Can look a bit B2C. Ensure the UI overlay looks professional and "enterprise-grade" to maintain authority.
Companies using similar video content -
Okta – Workforce Identity Cloud – Seamless verification for remote reality.
Duo Security (Cisco) – Trusted Access – Enables secure anywhere access.
20. The Velocity Gateway
BOFU | Objection Handling & Friction Reduction

The Visual & Narrative Approach
Visualization Scenario: The final hurdle is speed. We utilize a 2D animation composition where a stylized character in soft lavender and energetic yellow walks effortlessly through a digital doorway that slides open automatically. Floating UI elements like green ticks appear instantly as the character passes, signifying continuous, passive verification. The background features an abstract speed tunnel effect to emphasize velocity.
Narration Style: Fast and punchy. "Don't stop. Just go."
Psychological Impact & KPI Focus
- Niche Psychology: Directly counters "Security Fatigue." It promises a world where security is passive and invisible, rather than an active hurdle the user must jump over.
- Operational Impact: Visualizes Low Latency / Passive Auth. It demonstrates concepts like behavioral biometrics where the user is verified by how they act, not just what they know.
Strategic Implementation & Trade-offs
- Best Use: Retargeting Ad (for users who bounced from the pricing page).
- Duration: 6-10 Seconds.
- Trade-off: Over-promising. Ensure your product actually supports passive/continuous authentication before using this visual, or you risk disappointing the user during the demo.
Companies using similar video content -
Beyond Identity – Passwordless Authentication – Automated passage for frictionless entry.
Trusona – Frictionless Identity – Velocity gateway for continuous, passive verification.
21. The Integration Spark
Onboarding | Self-Serve Onboarding
The Visual & Narrative Approach
Visualization Scenario: Onboarding is where friction often kills adoption. We strip away the technical intimidation using a friendly, flat 2D vector style. A relatable character in a hoodie casually connects two giant, floating plug icons—one Red (representing the Legacy System/App) and one Blue (representing Your Platform). A spark of yellow energy buzzes between them as they snap together. The background is a clean, simplified tech office, emphasizing that this is a "human" task, not a "developer" task.
Narration Style: Encouraging and simple. "Connect your world. No PhD required."
Psychological Impact & KPI Focus
- Niche Psychology: Reduces "Configuration Anxiety." New users often fear breaking their existing setup. The playful, illustrative style signals that the process is safe, reversible, and user-friendly.
- Operational Impact: Visualizes Self-Service Capability. It empowers end-users or non-technical admins to perform integrations themselves, reducing the load on your implementation team.
Strategic Implementation & Trade-offs
- Best Use: In-App "Welcome" Modal / Onboarding Wizard.
- Duration: 15-20 Seconds.
- Trade-off: Tone Mismatch. If your brand is hyper-corporate/defense-oriented, this "startup hoodie" vibe might feel too casual. Ensure it aligns with your specific brand voice.
Companies using similar video content -
JumpCloud – Cloud Directory Platform – Plug-and-play setup for integration ease.
Gluu – Open Source Identity Platform – Character-driven story of simple integration.
22. The Value Velocity
Onboarding | Accelerating Time-to-Value

The Visual & Narrative Approach
Visualization Scenario: Speed is the ultimate feature. We create a high-energy montage where simplified UI screens in interface white layer and fly past the camera in 3D space. Motion blur streaks indicate velocity. The camera dives through these layers, landing abruptly but smoothly on a final, central screen displaying a large, pulsing green "Success" circle.
Narration Style: Fast-paced. "Setup? Done. Protection? Active. Value? Instant."
Psychological Impact & KPI Focus
- Niche Psychology: Appeals to the "Instant Gratification" desire. It visually promises that the investment of time to set up the software is minimal compared to the immediate output of security.
- Operational Impact: Visualizes Rapid Deployment. It serves as a visual counter-argument to the objection that enterprise security takes months to roll out.
Strategic Implementation & Trade-offs
- Best Use: "Welcome Aboard" Email / Post-Purchase Thank You Page.
- Duration: 10-15 Seconds.
- Trade-off: Detail Loss. The rapid cuts mean the user can't read the specific UI text. It sells the feeling of speed, not the details of the workflow.
Companies using similar video content -
Transmit Security – Identity Experience Platform – Rapid UI montage for accelerated value.
Descope – AuthN Platform – Interface velocity for instant security setup.
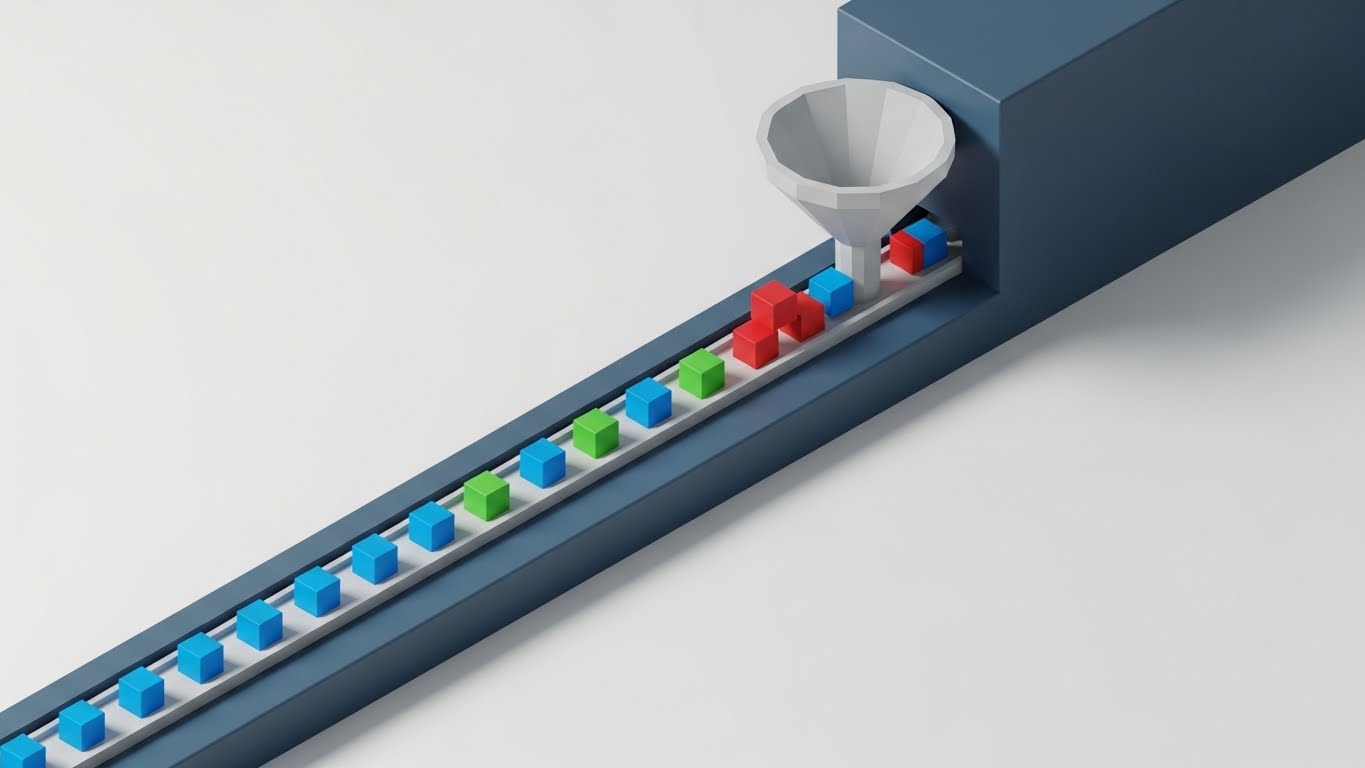
23. The Logic Flow
Onboarding | Reducing Implementation Friction
The Visual & Narrative Approach
Visualization Scenario: Documentation is often dry. We bring it to life with an isometric 3D animation. Small blue data cubes (user requests) flow smoothly along a track into a funnel-shaped filter (The Policy Engine). Red cubes bounce off the rim, while blue cubes pass through, turn green, and continue. The clean white surface and soft shadows create a sense of clinical precision and order.
Narration Style: Educational. "Visualizing the logic. You set the rules; we filter the noise."
Psychological Impact & KPI Focus
- Niche Psychology: Cognitive Fluency. It transforms complex logic trees (If/Then/Else policies) into a simple physical sorting process, making the configuration concepts easier to grasp.
- Operational Impact: Visualizes Policy Granularity. It demonstrates that the engine is capable of nuanced filtering, not just a binary "allow/block."
Strategic Implementation & Trade-offs
- Best Use: Knowledge Base Articles / Documentation Header.
- Duration: 20-30 Seconds (Looping).
- Trade-off: Abstraction. It is a metaphor for data processing. Technical architects may still require the actual flow charts or code snippets alongside this visual.
Companies using similar video content -
SailPoint – Identity Platform – Visualizes policy logic flow for clarity.
Saviynt – Enterprise Identity Cloud – Isometric workflow for implementation clarity.
24. The Cyberpunk Assistant
Retention | Reducing Support Overhead

The Visual & Narrative Approach
Visualization Scenario: Support doesn't have to look boring. We embrace a "Dark Mode" aesthetic appealing to developers and night-shift SOC analysts. A glowing, holographic chatbot avatar—formed from cyberpunk purple and laser red light particles—floats above a dark grid. It gestures intelligently towards a floating interface menu, guiding the user.
Narration Style: Futuristic. "Intelligent assistance. Standing by, 24/7."
Psychological Impact & KPI Focus
- Niche Psychology: Ingroup Bias. The "Dark Mode" aesthetic signals that you understand the developer/security culture. It feels like a tool built by hackers, for hackers.
- Operational Impact: Visualizes AI-Driven Support. It implies that the help available is automated, instant, and intelligent, rather than a slow human queue.
Strategic Implementation & Trade-offs
- Best Use: Help Center Landing Page / Chatbot Waiting Screen.
- Duration: 10-15 Seconds (Looping).
- Trade-off: Niche Appeal. This aesthetic is very specific to technical users. It might feel alienating or "too dark" for HR or Compliance managers.
Companies using similar video content -
SentinelOne – Singularity Platform – Cyberpunk assistant for tech-savvy support.
CrowdStrike – Falcon Platform – Futuristic neon support for security analysts.
25. The Culture of Trust
Retention | Reducing Churn

The Visual & Narrative Approach
Visualization Scenario: To retain customers, remind them of the human outcome. We use a bright, aspirational stock image of a diverse team in a modern, sunlit office. They are high-fiving or collaborating. Overlaid are subtle, glowing golden connectivity lines that weave between the people, representing the seamless, secure collaboration your software enables. The "Golden Hour" lighting evokes warmth and positivity.
Narration Style: Human-centric. "Security isn't just about locks. It's about opening doors for your team."
Psychological Impact & KPI Focus
- Niche Psychology: Social Belonging. It reframes the product from a "utility" to a "culture enabler." It reminds the buyer that good security builds a confident, productive workplace.
- Operational Impact: Visualizes Frictionless Collaboration. It reinforces that the MFA solution does not hinder teamwork but rather secures the connections between employees.
Strategic Implementation & Trade-offs
- Best Use: Customer Newsletter / Quarterly Business Review (QBR) Deck.
- Duration: Static Image or subtle Parallax.
- Trade-off: Stock Photo Risk. Must be high-quality. Low-budget stock photos can damage brand credibility. The "overlay" must look premium.
Companies using similar video content -
Okta – Workforce Identity Cloud – Fosters a culture of trust through human connectivity.
Microsoft Azure AD – Identity & Access Management – Aspirational montage for secure collaboration.
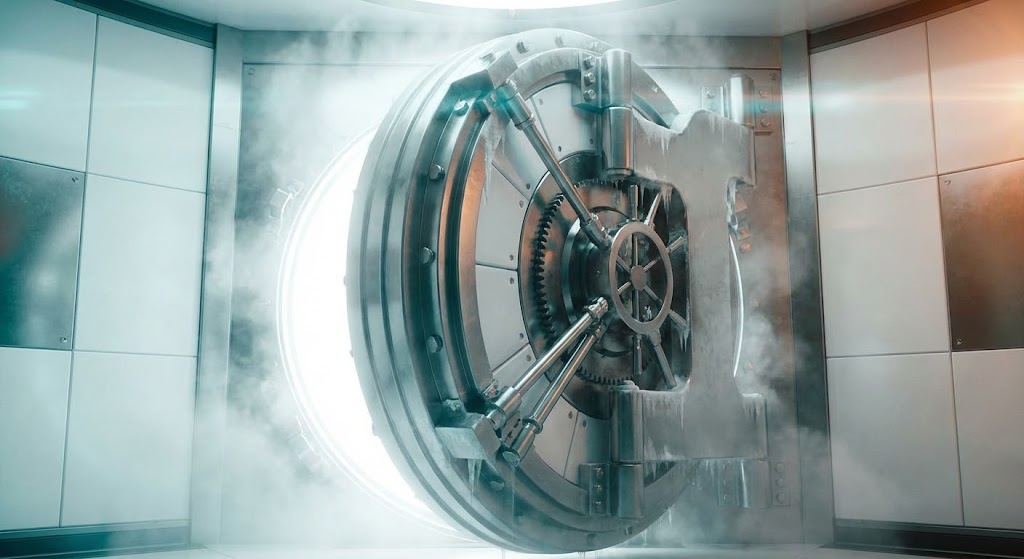
26. The Vault Reveal
Retention | Website Visitor Re-engagement
The Visual & Narrative Approach
Visualization Scenario: Sometimes, you need drama to re-engage a dormant user. We use a cinematic, photorealistic render of a massive circular vault door made of white ceramic and titanium. As it slowly rolls open, blindingly pure white light spills out, silhouetting the heavy locking mechanisms. Volumetric fog and teal/orange grading give it a movie-trailer quality.
Narration Style: Epic. "The standard has been raised. Welcome to the new fortress."
Psychological Impact & KPI Focus
- Niche Psychology: Awe and Authority. The sheer scale and weight of the vault door command respect. It signals a major upgrade or a feature release that is too important to ignore.
- Operational Impact: Visualizes Impenetrability. It is a metaphor for the strength of the backend security, designed to reignite interest in the platform's capabilities.
Strategic Implementation & Trade-offs
- Best Use: Feature Announcement Video (YouTube) / Re-engagement Email Header.
- Duration: 10-15 Seconds.
- Trade-off: Hype vs. Reality. Use this only for major updates. Using a vault door reveal for a minor bug fix will lead to disappointment.
Companies using similar video content -
CyberArk – Identity Security Platform – Cinematic vault reveal for dramatized security.
Thales – CipherTrust Data Security Platform – Reveals the ultimate data security vault.
27. The Deep Dive
Expansion | Driving Deep Feature Adoption

The Visual & Narrative Approach
Visualization Scenario: To upsell advanced features, we show depth. We use a 3D parallax effect where translucent UI windows float at different depth layers. The front layer is sharp, displaying "Advanced Settings" sliders in crisp white. The background layers are blurred representations of code or raw data. The camera moves laterally, emphasizing the separation and the "deep" control available.
Narration Style: Sophisticated. "Go deeper. Fine-tune every variable."
Psychological Impact & KPI Focus
- Niche Psychology: Perceived Control. Advanced users want to feel like they can tweak the engine. The 3D layers visually represent "Defense in Depth" and granular control.
- Operational Impact: Visualizes Configurability. It demonstrates that the platform is not a "black box" but a layered system that adapts to complex enterprise needs.
Strategic Implementation & Trade-offs
- Best Use: "Pro Feature" Spotlight / Product Update Blog.
- Duration: 8-12 Seconds (Looping).
- Trade-off: Visual Complexity. Can be overwhelming for a basic user. Target this specifically at Admins/Power Users who crave this level of detail.
Companies using similar video content -
Ping Identity – Intelligent Identity Platform – Deep dive into advanced configuration.
ForgeRock – Identity Platform – 3D parallax UI for interface depth.
28. The Global Overseer
Expansion | Driving Upsell/Cross-sell

The Visual & Narrative Approach
Visualization Scenario: Selling to the Enterprise means selling global scale. A realistic 3D globe spins slowly in the center. Hovering over it is a curved, translucent blue holographic interface showing connection lines spanning continents (e.g., New York to Tokyo). As the lines connect, they turn "Map Green." The aesthetic is command-center chic.
Narration Style: Grandiose. "One dashboard. No borders. Global identity secured."
Psychological Impact & KPI Focus
- Niche Psychology: Scalability Assurance. It addresses the anxiety of multinational CIOs: "Can this handle my APAC and EMEA divisions simultaneously?"
- Operational Impact: Visualizes Geo-Redundancy & Global Reach. It implies that the authentication fabric is worldwide, justifying an upsell to an "Enterprise" plan.
Strategic Implementation & Trade-offs
- Best Use: Sales Deck (Enterprise Tier Slide) / ABM Campaign.
- Duration: 15-20 Seconds (Looping).
- Trade-off: Enterprise Only. This visual is irrelevant for SMBs. Use strictly for large account expansion.
Companies using similar video content -
IBM Security Verify – Identity as a Service – Holographic UI for global oversight.
AWS IAM – Identity and Access Management – Global overseer for enterprise expansion.
29. The Viral Network
Expansion | Driving Referrals & Advocacy
The Visual & Narrative Approach
Visualization Scenario: Growth should feel organic. We use a low-poly 3D style where a central node (a faceted crystal in teal) connects to three others. These nodes light up and spawn their own connections, creating a rapidly expanding, stable crystalline structure. The pastel colors and soft lighting make the growth feel natural and positive, rather than aggressive.
Narration Style: Community-focused. "Stronger together. Build the network of trust."
Psychological Impact & KPI Focus
- Niche Psychology: Network Effects. It visualizes the concept that security is better when shared. It subtly encourages the user to invite partners or subsidiaries into the ecosystem.
- Operational Impact: Visualizes Ecosystem Integration. It represents the "Partner Program" or "Vendor Portal" features, encouraging the user to invite others.
Strategic Implementation & Trade-offs
- Best Use: Referral Program Page / Partner Portal.
- Duration: 10-15 Seconds (Looping).
- Trade-off: Abstract. It represents the concept of growth, not the mechanism of a referral. Best used as a background element.
Companies using similar video content -
Keycloak – Open Source Identity and Access Management – Organic network for viral advocacy.
Gluu – Open Source Identity Platform – Low-poly 3D modeling of a growing network.
30. The Pulse of Innovation
Expansion | Proactive Support/Announcements

The Visual & Narrative Approach
Visualization Scenario: Your platform is alive and evolving. We use hyper-lapse aerial footage of a busy city skyline at night. Fast-moving traffic creates streaks of light. Superimposed over this reality are crisp white data streams connecting the skyscrapers, pulsing rhythmically. It conveys a sense of non-stop activity, speed, and modern infrastructure.
Narration Style: Dynamic. "The city never sleeps. Neither do we."
Psychological Impact & KPI Focus
- Niche Psychology: Vitality and Future-Proofing. It reassures the customer that they are subscribed to a living, breathing service that keeps pace with the modern world.
- Operational Impact: Visualizes Real-Time Monitoring. The "pulse" implies active, continuous scanning and protection, reinforcing the value of the subscription.
Strategic Implementation & Trade-offs
- Best Use: "Year in Review" Video / Major Version Release Background.
- Duration: 15-30 Seconds.
- Trade-off: Generic Tech Vibe. It can look like a generic telecom ad if the data overlays aren't sharp and brand-specific.
Strategic Knowledge Base: The Visual Operations Doctrine
To bridge the gap between "Visual Style" and "Business Outcomes," we present a synthesized framework for operationalizing these assets. This is not just about making things look good; it is about using visual strategy to drive adoption, compliance, and ROI in the identity security sector.
Strategic Alignment & Visual Architecture
The "Pre-Production" Strategy – Why and Who.
- The Cognitive Load Audit: Before creating a single pixel, audit the "Cognitive Load" of your current MFA setup process. Identify where users hesitate. Deploy the simplest styles (e.g., Style 3: Biometric Morph) specifically at these high-friction points to reduce abandonment.
- Role-Based Visual Mapping: Do not use the same visuals for everyone. Map Style 21 (Friendly/Simple) to End-Users to lower anxiety, while reserving Style 14 (Admin Zen) and Style 27 (Parallax UI) for IT Administrators who need to feel in control of the complexity.
- The "Glanceability" Standard: In security, seconds matter. Design authentication prompts and icons (like Style 10: Tactile Toggle) to be understood in under 500ms. If the user has to read a paragraph to understand a security prompt, the visual architecture has failed.
- Brand Voice Consistency: Your security tools are an extension of your brand. Ensure that the "Invisible Shield" aesthetic (Style 1) is consistent across the login screen, the admin panel, and the mobile app. Disjointed visuals create mistrust.
- The Advids Strategic Audit: Engaging a partner like Advids early allows you to define this "Visual Operating System" comprehensively. We help you build a visual lexicon that scales, ensuring your "Checkmark" looks the same in a sales deck as it does in the product UI.
- Standardization vs. Customization: For core icons (Lock, Key, Shield), use standardized, recognizable forms (Style 16: Modular Blockade) to leverage existing user mental models. Reserve bespoke, high-end visualization (Style 7: Digital Iris) for your unique value propositions (UVPs).
- The Cross-Departmental Bridge: Use these visuals to align your internal teams. Sales should be showing the same visuals (Style 12: Titanium Token) that Product is building and Support is documenting. This unifies the customer experience from prospect to power user.
- Legacy System Integration: Visualizing the invisible bridge between on-premise Legacy AD and Cloud IDP is critical. Use Style 11 (The Clarifying Line) to visually demonstrate how your platform bridges the gap without ripping and replacing infrastructure.
- Accessibility in Identity: Ensure that color-coded cues (Red/Green) in styles like Style 9 (Verification Factory) are accompanied by shape changes or motion to remain accessible to color-blind users. Security must be inclusive.
- The Mobile-First Mandate: With the rise of push-notification MFA, every visual style must be legible on a 6-inch screen. Optimize Style 19 (Anywhere Access) to ensure your brand trust translates to mobile devices.
Operational Adoption & Implementation
The "Deployment" Phase – How to embed visuals into the workflow.
- Overcoming "Privacy" Anxiety: Adoption stalls when users fear surveillance. Use empathy-driven visuals (Style 7: Digital Iris) to explain that biometric data is hashed and stored locally, not "watched" by the company. Visual transparency builds trust.
- The Micro-Learning Shift: Users will not read a 20-page PDF on FIDO2 compliance. Replace manuals with a library of 15-second Micro-Learning clips (using Style 22: Rapid UI) embedded directly into the onboarding email flow.
- Just-in-Time Support: Embed specific visual loops (like Style 23: Isometric Workflow) directly into error messages or tooltips. When a user fails a login, show them visually why it happened and how to fix it immediately.
- Gamification of Security: Use Style 22 (Success Circles) to visualize "Security Scores" or "Setup Completion." Visual progress bars and celebration animations trigger dopamine, encouraging users to complete security hygiene tasks.
- Reducing Support Ticket Volume: There is a direct correlation between proactive visual guides and reduced Help Desk volume. Implementing Style 24 (Cyberpunk Assistant) in your help center can deflect Tier-1 tickets by answering "How-to" questions visually.
- Remote Onboarding: In a distributed workforce, you cannot hold in-person security seminars. Use Style 25 (Aspirational Stock) and screen-cast hybrids to create a "warm" remote onboarding experience that feels personal and high-touch.
- Standard Operating Procedures (SOPs): Transform text-heavy compliance SOPs into visual process flows using Style 2 (Blueprint to Reality). This ensures that complex protocols are followed precisely by SOC teams.
- Feedback Loops: Use interactive video elements to gather user sentiment. A simple "Thumbs Up/Down" overlay on a tutorial video provides data on whether your visual strategy is actually helping users.
- Scalable Localization: Cyber threats are global; your visuals must be too. By using abstract, text-free styles like Style 8 (The Neural Brain), you create assets that require zero translation for your international subsidiaries.
- Leadership Communication: CISOs need to sell security strategy to the Board. Equip them with high-end, cinematic assets like Style 26 (The Vault Reveal) to communicate the robustness of the security posture during quarterly reviews.
Measuring Impact & Future-Proofing
The "ROI" Phase – Measuring success and looking ahead.
- Beyond "Views": Do not measure video success by "views." Measure it by "Time-to-Competency" (how fast a new user sends their first secured message) or "Feature Adoption Rate" (how many users enabled MFA after watching).
- The "Friction Metric": Correlate visual intervention with the "Friction Index." If users watching the Style 21 onboarding video have a 20% higher completion rate than those who don't, you have proven ROI.
- Compliance Velocity: Measure how quickly your organization adapts to new mandates (e.g., NIST, GDPR). Visual training (Style 13: Enterprise Fortress) accelerates the dissemination of new compliance standards across the workforce.
- Retention and Churn: High-quality UX visualization is a switching cost. If your platform feels "easier" and "cleaner" (thanks to Style 14: Admin Zen) than the competitor, customers are less likely to churn.
- The AI Visual Frontier: Prepare for the future where threat visualization is generated in real-time by AI. Styles like Style 8 (Neural Brain) set the stage for these advanced, data-driven interfaces.
- Scalability of Assets: Build a modular asset library. Don't create "one-off" videos. Create a system of backgrounds, icons, and motion behaviors that can be reassembled into new features.
- The Advids Partnership: Advids acts as your long-term visual partner, maintaining this library and ensuring that as your product evolves from V1 to V10, your visual language evolves seamlessly with it, protecting your brand equity.
- Benchmarking Success: Compare your "Visual Fluency" against competitors. In a crowded SaaS market, the vendor that explains the solution the fastest (using Style 11: The Clarifying Line) often wins the RFP.
- The ROI of Prevention: Quantify the value of "breaches avoided." Better visual training leads to fewer phishing clicks. Frame your visual budget as an investment in risk mitigation, not just marketing content.
- Final Call to Innovation: Treat video and motion design not as "content," but as "infrastructure." In a Zero-Trust world, the Visual Interface is the only thing the user touches. Make it as robust, secure, and performant as the code underneath.
[END OF GUIDE]
Companies using similar video content -
SentinelOne – Singularity Platform – Data pulse for proactive vitality and innovation.
Palo Alto Networks – Cortex XDR – Hyper-lapse footage showing the pulse of innovation.

 /home/wwwroot/advids.co/design/index.php on line 425
/home/wwwroot/advids.co/design/index.php on line 425