Introduction: Closing the Remediation Gap Through Visualization
The cybersecurity industry has mastered the art of detection. We have moved from a lack of visibility to an overwhelming surplus of it. Today’s Security Operations Centers (SOCs) are not struggling to find vulnerabilities; they are struggling to fix them before they are exploited. This is the "Remediation Gap"—the dangerous latency between the digital detection of a threat and the operational act of applying a patch.
For the modern CISO, the enemy is no longer just the attacker; it is time. Recent industry data reveals a startling reality: critical vulnerabilities take 4.5 months on average to remediate. This delay acts as an open invitation to adversaries, creating a window of exposure that far exceeds acceptable risk tolerances.
This guide is not merely a collection of aesthetic choices; it is a strategic framework designed to visualize the bridge across that remediation gap. The business case for doing so is undeniable: organizations that apply security AI and automation extensively save $2.22 million per breach. By moving away from alarmist "hacker in a hoodie" stock imagery and embracing precise, data-driven visualization styles, we can articulate the value of automated remediation, risk prioritization, and seamless endpoint protection.
The following visual strategies are engineered to lower cognitive load, build immediate trust, and demonstrate—with absolute clarity—how your platform turns chaotic vulnerability data into decisive security action.
1. Abstract 2D Flat Vector Organic
TOFU | Brand Awareness

The Visual & Narrative Approach
Scenario: The frame opens on a clean, lightbox-lit environment where fluid, amorphous shapes in vivid Coral and Soft White float effortlessly. These abstract forms represent the chaotic, ever-changing nature of the digital attack surface. As the narrative progresses, these shapes naturally coalesce and morph into a solid, structured protective shield in the center of the frame. The movement is smooth and liquid, visualizing the "self-healing" capabilities of an automated vulnerability management system.
Narration: The tone is calm, sophisticated, and reassuring. It avoids alarmist language, focusing instead on the elegance of fluid adaptation and the peace of mind that comes from continuous protection.
Psychological Impact & KPI Focus
Niche Psychology: Security leaders suffer from "alert fatigue." This style utilizes organic shapes and soft gradients to reduce Cognitive Load, signaling that the platform is an antidote to chaos, not a source of more noise. It appeals to the desire for a system that "just works" in the background.
Operational Impact: Visually reinforces the concept of Continuous Monitoring. By showing the shield constantly reforming without visible human intervention, it subtly communicates the benefit of automated, 24/7 coverage.
Strategic Implementation & Trade-offs
Use Cases: Ideal for high-level "Hero" sections on the website homepage or introductory brand videos where the goal is to establish a modern, approachable identity.
Duration: 15–30 seconds.
Trade-offs: Abstract Nature. While visually stunning, this style is low on technical detail. It establishes feeling and brand, but it does not explain how the technology works.
Companies using similar video content -
Snyk – AI Security Platform – Fluidly adapts to secure evolving codebases.
Darktrace – Enterprise Immune System – Autonomous AI detects and responds to threats.
2. Isometric 2D Motion Design
TOFU | Market Education

The Visual & Narrative Approach
Scenario: We view a pristine white digital grid from a 45-degree high angle. White architectural towers, representing servers, are arranged in a structured pattern. Some towers have visible gaps or "holes." Blocks of Signal Orange geometric shapes slide rapidly along the grid lines, automatically slotting into these gaps with a satisfying snap. This mechanical precision visualizes "Patch Automation"—the orange blocks are the patches, and the towers are the assets being hardened.
Narration: The voiceover is precise, rhythmic, and instructional. It emphasizes words like "structure," "alignment," and "integration," mirroring the snapping motion of the visuals.
Psychological Impact & KPI Focus
Niche Psychology: IT Directors crave order and predictability. The isometric grid provides a sense of absolute control and total visibility. The sharp shadows and clean lines signal that the platform is precise and leaves no room for error.
Operational Impact: Directly addresses the Remediation Gap. The visual metaphor of the "block" instantly filling the "hole" simplifies the complex process of patch deployment into a singular, understandable action, reinforcing MTTR (Mean Time to Remediate) reduction.
Strategic Implementation & Trade-offs
Use Cases: Explainer videos on "How it Works" pages or educational blog posts about patch management architecture.
Duration: 45–60 seconds.
Trade-offs: Emotional Distance. The style is very clinical and "cool." It builds authority but may lack the human element required for emotional connection.
Companies using similar video content -
Qualys – Vulnerability Management (VMDR) – Cloud-based platform for comprehensive vulnerability management.
Rapid7 – InsightVM – Advanced vulnerability management with real-time risk visibility.
4. Bold Kinetic Typography (Visual)
TOFU | YouTube

The Visual & Narrative Approach
Scenario: The screen is dominated by heavy geometric shapes in Bright Lime and Charcoal instead of traditional letters. Fast-moving shapes collide and swarm in chaos before hitting an invisible barrier and instantly snapping into a rigid, organized grid on a Stark White background. This aggressive transition from chaos to order visualizes "Risk Remediation"—the instant stabilization of a volatile environment. The style mirrors Swiss Design: objective, legible, and highly organized.
Narration: Fast-paced, energetic, and confident. The audio design is crucial here—heavy "whoosh" and "click" sound effects accentuate the speed of the transition.
Psychological Impact & KPI Focus
Niche Psychology: Targets the "Need for Speed." Security incidents move fast, and this style assures the viewer that the platform moves faster. It appeals to the Action-Oriented persona who values speed above all else.
Operational Impact: Visualizes Incident Response Velocity. The speed of the animation serves as a direct metaphor for the platform's processing speed, promising a reduction in the window of exposure.
Strategic Implementation & Trade-offs
Use Cases: YouTube "Hook" intros or social media teaser ads designed to stop the scroll. Excellent for announcing new feature launches.
Duration: 6–12 seconds.
Trade-offs: Comprehension Risk. Without voiceover or supporting text, the abstract shapes might be interpreted in various ways. It captures attention but relies on context.
Companies using similar video content -
OpenText – ArcSight SOAR – Integrates security tools into optimized threat response workflows.
5. Minimalist Flat 2D Vector
TOFU | Vertical Social Organic

The Visual & Narrative Approach
Scenario: A macro, close-up shot of a single stylistic element: a stylized padlock in Pastel Pink and Slate Blue. The background is a calming Cream color. In a seamless, looped animation, the shackle of the padlock rotates and transforms the entire body of the lock into a green "Checkmark." The animation is slow and deliberate, emphasizing ease and finality.
Narration: Minimal or non-existent. Soft, lo-fi beats or ambient sound. The visual tells the entire story: "Locked = Done."
Psychological Impact & KPI Focus
Niche Psychology: Addresses the "Complexity Overload" of security tools. By reducing the concept of Endpoint Protection to a single, friendly icon, it lowers the barrier to entry and positions the product as approachable and user-friendly.
Operational Impact: Highlights Compliance Achievement. The checkmark is the universal symbol for "Audit Passed" or "System Secure," reinforcing the platform's role in maintaining continuous compliance posture.
Strategic Implementation & Trade-offs
Use Cases: Instagram Reels, TikTok, or LinkedIn Stories. Perfect for mobile consumption where screen real estate is limited.
Duration: 15 seconds (Looping).
Trade-offs: Depth Limitation. This style cannot convey complex technical differentiators. It is purely a sentiment builder.
Companies using similar video content -
Torq – Hyperautomation – Accelerates SecOps workflows with multi-agent AI.
Cybereason – Defense Platform – Intercepts threats earlier with MalOps detection.
6. Abstract 2D Motion Graphics
TOFU | Skippable Pre-Roll Ad

The Visual & Narrative Approach
Scenario: Utilizing a geometric "Memphis" style (as seen in the reference image), we visualize the sorting of complex data. A chaotic stream of Yellow circles, Blue triangles, and Black squares (representing raw threat data) flows across the screen. As they pass through a central filtering line, they self-organize into neat, parallel rows of uniform shapes. This abstractly visualizes "Threat Intelligence"—the separation of critical signals from noise.
Narration: A deep, resonant voiceover that cuts through the visual noise. "Stop drowning in data. Start seeing the truth."
Psychological Impact & KPI Focus
Niche Psychology: Directly targets Alert Fatigue. The visual of "sorting" and "organizing" is cathartic for a security analyst who spends their day sifting through false positives. It promises clarity and focus.
Operational Impact: Visualizes False Positive Reduction. The transformation from chaotic shapes to organized rows illustrates the efficiency gain of using the platform's AI prioritization.
Strategic Implementation & Trade-offs
Use Cases: Pre-roll ads on tech news sites or YouTube. The high contrast and movement capture the eye immediately.
Duration: 15–20 seconds.
Trade-offs: Generic Potential. To succeed, the "filtering" moment must be distinct and clearly linked to the concept of intelligence.
Companies using similar video content -
Vanta – Compliance Automation – Automates continuous controls monitoring for compliance.
Drata – Compliance Automation – Streamlines GRC with automated security and compliance.
7. Dynamic Data Visualization
MOFU | Demand Gen & Lead Capture

The Visual & Narrative Approach
Scenario: In a clean white void, a 3D bar chart extrudes upwards from a glass-like base. The camera focuses on the height differences. The tallest bars, representing critical risks, glow with an intense Gold inner light. The shorter, less critical bars are a cool Emerald Green. A "glassmorphism" effect blurs the background, keeping the focus strictly on the data peaks. As the camera pans, the Gold bars are "clicked" and resolve down, visualizing the prioritization and resolution process.
Narration: Professional, analytical, and data-centric. "Prioritize based on business context, not just CVSS scores."
Psychological Impact & KPI Focus
Niche Psychology: Appeals to the "Quantified Executive." CISOs need to report to the Board in numbers, not feelings. This style elevates the dashboard to an art form, suggesting that the platform provides board-ready insights.
Operational Impact: Visualizes Risk Prioritization. The use of height and color (Gold vs. Green) clearly demonstrates the platform's ability to distinguish between a critical vulnerability and a minor bug.
Strategic Implementation & Trade-offs
Use Cases: Whitepaper download landing pages, webinar backdrops, or "Features" pages focusing on reporting capabilities.
Duration: 30–45 seconds.
Trade-offs: Perceived Complexity. The visualization must remain clean and not overcrowded with data points to avoid overwhelming the viewer.
Companies using similar video content -
Google – SecOps – Uses AI to prioritize alerts and contextualize threats.
Splunk – Security Cloud – Collects, monitors, and analyzes machine data for threat detection.
8. Rapid UI Feature Montage
MOFU | Feature Education

The Visual & Narrative Approach
Scenario: Floating abstract UI cards—simplified representations of the platform's dashboard—hover in a dark space. They are colored in Sky Blue, Navy, and Safety Yellow. Snap-lines (bright connectors) rapidly draw themselves between the cards, linking a "Vulnerability Found" card to an "Automated Ticket" card and finally to a "Patch Deployed" card. The camera moves dynamically, following the lines as they snap into place, creating a sense of a cohesive ecosystem assembling itself.
Narration: Upbeat and fast. "Connect. Automate. Resolve." The pacing matches the "snap" of the UI connections.
Psychological Impact & KPI Focus
Niche Psychology: Targets the frustration of "Siloed Tools." Security teams often use disjointed stacks. This style visualizes integration and ecosystem, reassuring the viewer that this platform plays well with others (JIRA, ServiceNow, etc.).
Operational Impact: Visualizes Automated Workflows. The visible connection lines represent the APIs and logic flows that replace manual email chains and spreadsheets.
Strategic Implementation & Trade-offs
Use Cases: Product tour videos, demo intros, and feature highlight reels.
Duration: 45–60 seconds.
Trade-offs: Pacing Issues. Requires a balance between "high energy" and "readability."
Companies using similar video content -
Axonius – Cybersecurity Asset Management Platform – Unifies asset inventory, uncovers security gaps.
Tenable.io – Vulnerability Management Platform – Proactively identifies and remediates vulnerabilities.
9. Photorealistic 3D Renders
MOFU | Building Trust & Credibility

The Visual & Narrative Approach
Scenario: A wide-angle, cinematic shot of a futuristic server room. The environment is pristine—floor-to-ceiling glass, Cool White ambient lighting, and rows of server racks with Brushed Aluminum textures. A subtle Laser Red status light pulses gently on one rack, which then turns to a solid, calm Blue. The camera moves slowly, creating a sense of weight, scale, and physical reality.
Narration: Gravitas-filled and serious. "Your infrastructure is the backbone of your business. Protect it with the precision it deserves."
Psychological Impact & KPI Focus
Niche Psychology: Anchors the software in reality. SaaS can feel intangible. This style reminds the viewer of the physical assets they are protecting—expensive, critical hardware. It builds high-end credibility and trust (the "Bank Vault" effect).
Operational Impact: Visualizes Server Hardening. The transition from Red light to Blue light is a subtle but powerful cue for "Threat Neutralized" in the physical domain.
Strategic Implementation & Trade-offs
Use Cases: Trust Center pages, "About Us" brand videos, and high-stakes investor presentations.
Duration: 30–60 seconds.
Trade-offs: Production Cost. This is the most expensive style to produce. It must be executed flawlessly to avoid looking "cheap."
Companies using similar video content -
Palo Alto Networks – Cortex XSOAR – Integrates AI, analytics, automation, and orchestration.
Swimlane – Turbine – Unifies security operations with AI-enabled, low-code automation.
10. 2D Line Art Animation
MOFU | Overcoming Objections

The Visual & Narrative Approach
Scenario: A close-up of a White paper texture background. A single, continuous line in Gold ink draws a tangled, chaotic knot in the center. As the animation plays, the line gracefully untangles itself, flowing outwards to become a perfectly straight, smooth horizon line. Black ink accents mark key milestones along the straight line. This visualizes the simplification of a complex "Incident Response" process.
Narration: Soft, consultative, and wise. "Complexity is the enemy of security. We straighten the path."
Psychological Impact & KPI Focus
Niche Psychology: Addresses the fear of "Spaghetti Workflows." Incident response often feels messy and panicked. This style projects sophistication and calm, suggesting that the vendor has a "Zen-like" mastery over the chaos.
Operational Impact: Visualizes Process Optimization. The "unraveling" metaphor is perfect for explaining how the platform simplifies complex dependency chains or compliance audits.
Strategic Implementation & Trade-offs
Use Cases: "Philosophy" or "Methodology" sections of the website, or videos addressing specific objections about implementation difficulty.
Duration: 45–90 seconds.
Trade-offs: Low Excitement. This style is intellectual, not visceral. It works well for thoughtful decision-makers but may bore a technical practitioner looking for feature specs.
Companies using similar video content -
Claroty – The Claroty Platform – Protects cyber-physical systems and mission-critical infrastructure.
Nozomi Networks – Nozomi Networks Platform – Safeguards critical infrastructure from cyber threats.
11. 3D X-Ray Visualization
MOFU | Risk Mitigation

The Visual & Narrative Approach
Scenario: The camera performs a slow, clinical macro zoom into a stylized high-tech processor or server blade. The outer shell is rendered in "Translucent Blue," revealing the complex multi-layered architecture within. Amidst the orderly green circuitry, a glowing Orange anomaly—representing a "Zero Day Threat"—pulsates deep in the dependency stack. A digital containment field (wireframe cage) instantly forms around the anomaly, physically isolating it from the healthy data pathways.
Narration: Diagnostic and precise. "Surface scanning is no longer enough. See deep into your dependencies. Isolate the unknown before it executes."
Psychological Impact & KPI Focus
Niche Psychology: Targets the "Paranoia of the Unknown." Security architects know that the most dangerous threats (like Log4j) are often buried deep in firmware or libraries. This "X-Ray" aesthetic satisfies the need for Deep Visibility, reassuring the viewer that the platform looks deeper than standard surface-level scanners.
Operational Impact: Visualizes Zero-Day Mitigation. The act of "isolating" the pulsing orange node physically demonstrates the concept of containment and micro-segmentation, directly linking to MTTC (Mean Time to Contain).
Strategic Implementation & Trade-offs
Use Cases: "Technology" deep-dive pages, whitepapers on "Runtime Security," and technical webinars.
Duration: 20–30 seconds.
Trade-offs: High Technical Bar. This style assumes a level of technical literacy. It appeals to the practitioner but may be too abstract for a non-technical financial buyer.
Companies using similar video content -
D3 Security – Smart SOAR – Transforms security operations with automation and MITRE ATT&CK.
Tufin – Network Segmentation – Tightens security and ensures compliance across hybrid networks.
13. Lifestyle Stock with UI Overlay
MOFU | LinkedIn Organic

The Visual & Narrative Approach
Scenario: A high-quality cinematic shot of a CISO or SecOps Director in a modern, sunlit office. The lighting is natural "Golden Hour," contrasting with the typical dark, blue-lit security imagery. She looks over her shoulder with a confident smile, holding a tablet. Superimposed and tracked onto the device screen is a crisp, simplified dashboard interface in Warm Beige and Navy. It shows a "Risk Score" dropping and a "Compliance" dial hitting 100%.
Narration: Empathetic and empowering. "Control doesn't require a war room. It requires the right lens. Security that works for you, anywhere."
Psychological Impact & KPI Focus
Niche Psychology: Targets the Burnout Crisis endemic in the industry. By showing a relaxed, smiling professional in a natural environment, it subliminally promises a better work-life balance and a move away from "firefighting" mode.
Operational Impact: Visualizes Real-Time Accessibility. It demonstrates that critical risk data is available at the executive's fingertips, not locked in a SOC control room, facilitating faster, data-driven decision-making.
Strategic Implementation & Trade-offs
Use Cases: LinkedIn organic posts, recruitment videos, and "Life at [Company]" culture assets.
Duration: 15–20 seconds (Looping).
Trade-offs: Generic Risk. Without the specific UI overlay, it is just a stock photo. The UI tracking must be premium and clearly relevant to security to maintain authority.
Companies using similar video content -
Snyk – Container – Keeps base images secure with container and Kubernetes security.
SentinelOne – Singularity XDR – Automates threat detection and response across workloads.
14. Hyper-lapse Stock Footage
MOFU | Non-Skippable Ads

The Visual & Narrative Approach
Scenario: An aerial drone shot of a sprawling city highway system at night. The physical cars are replaced by streaming lines of light—Cyan for safe traffic, Magenta for suspicious packets. As the traffic flows, we see the streams physically separating onto different highway levels, visualized as "Lanes." A rogue red stream attempts to change lanes but is blocked by a digital barrier. This visualizes "Network Segmentation"—keeping critical data in the fast lane and diverting threats.
Narration: Grand and rhythmic. "Traffic flows. Threats don't. Segment your network with the speed of the city."
Psychological Impact & KPI Focus
Niche Psychology: Enterprise networks are massive and chaotic. This style provides a sense of Scale and Governance. It reassures the viewer that the platform can handle high-throughput environments (global scale) without choking performance.
Operational Impact: Visualizes Lateral Movement Prevention. It translates the abstract concept of "firewall rules" into the physical reality of highway infrastructure, making the concept of "East-West" traffic control immediately intuitive.
Strategic Implementation & Trade-offs
Use Cases: Background loops for trade show booths (large format screens) or high-impact pre-roll ads where sound might be off.
Duration: 10–20 seconds (Loopable).
Trade-offs: Metaphor Reliance. It is a pure metaphor. It builds feeling and scale but does not show the actual UI or specific features.
Companies using similar video content -
Imperum – Autonomous SecOps & Investigation Platform – Unifies detection, investigation, and response.
15. Wireframe to Reality Transition
BOFU | Product/Solution Differentiation
The Visual & Narrative Approach
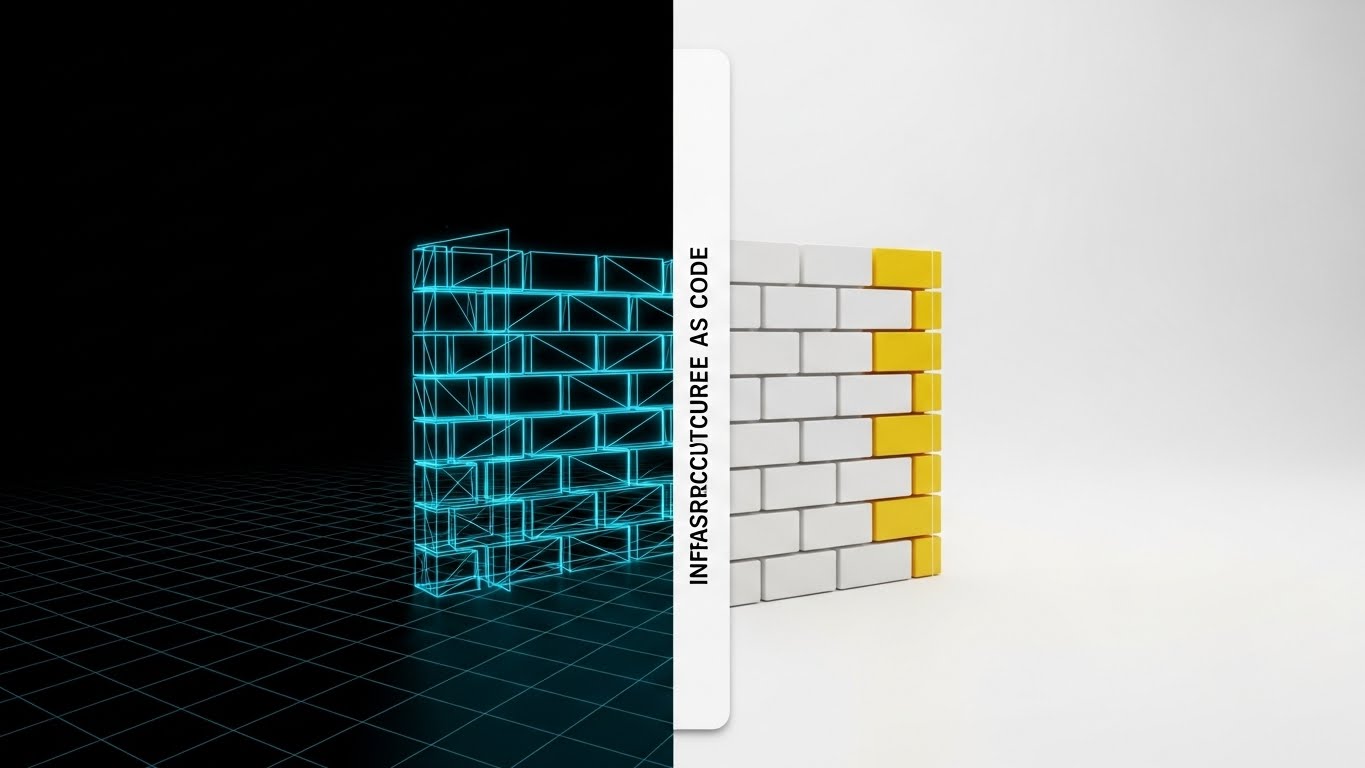
Scenario: A split-screen composition. The left side displays a digital "blueprint" wireframe of a firewall structure being drawn in "Blueprint Blue" lines. As the lines cross a central vertical threshold to the right, they instantly solidify into a robust, physical wall of White and "Construction Yellow" bricks. This sliding transition visualizes the concept of "Infrastructure as Code" (IaC)—where the security plan (code) becomes the physical reality instantly.
Narration: Constructive and definitive. "Don't just plan security. Build it. From code to concrete, in milliseconds."
Psychological Impact & KPI Focus
Niche Psychology: Targets the DevSecOps persona. They want security "shifted left" (handled early in development). This visual proves the platform understands modern engineering workflows, where security is built, not bought.
Operational Impact: Visualizes Immutable Infrastructure. The solid brick wall represents the unshakeable nature of code-defined security policies, contrasting with the fragility of manual configuration drift.
Strategic Implementation & Trade-offs
Use Cases: Technical solution pages, integration partner announcements (e.g., "Now integrated with Terraform"), and developer documentation intros.
Duration: 20–30 seconds.
Trade-offs: Niche Appeal. This is highly specific to modern, cloud-native organizations. Legacy IT teams might find the "code" aspect less relevant.
Companies using similar video content -
CrowdStrike – Falcon – Cloud-delivered EDR with AI-powered protection.
Microsoft – Defender for Endpoint – Provides preventative protection and automated investigation.
16. Split Screen: Optimized Reality
BOFU | ROI Justification

The Visual & Narrative Approach
Scenario: A split screen designed to connect human effort with business results. On the left, high-quality footage of an IT Administrator in a server room, smiling and closing a laptop—the universal sign of "job done." On the right, a crisp, animated Green trend line on a white background spikes upward, labeled "ROI Optimization." The visual timing is synced: as the admin smiles, the chart spikes.
Narration: Professional and results-oriented. "Efficient teams drive efficient growth. Reclaim time, reduce cost, and prove value."
Psychological Impact & KPI Focus
Niche Psychology: Bridges the gap between Operations and Finance. The CISO needs to justify the budget to the CFO. This style provides the visual evidence that "Happy/Efficient Security Team = Profitable Business." It humanizes the ROI calculation.
Operational Impact: Visualizes Operational Efficiency Gains. It explicitly links the reduction of manual toil (the admin finishing early) to the increase in business value, addressing the "Cost Center" stigma of security teams.
Strategic Implementation & Trade-offs
Use Cases: Case study summary videos, "Why Us" pages, and final-stage sales presentation decks.
Duration: 30–45 seconds.
Trade-offs: Simplicity. It simplifies a complex correlation. It works best as a summary statement, not a detailed proof.
Companies using similar video content -
Zscaler – Workload Segmentation – Host-based microsegmentation emphasizing zero trust.
Akamai – Guardicore Segmentation – Software-based microsegmentation to stop lateral movement.
17. Futuristic Neon/Dark Mode
BOFU | Competitive Displacement

The Visual & Narrative Approach
Scenario: A cyberpunk-inspired scene. A heavy, metallic digital vault floats in a Deep Purple void. Neon Magenta laser beams crisscross aggressively in front of the vault door, forming an impenetrable net. This visualizes "Active Prevention"—not just a lock, but an active defense system. The camera utilizes a Dutch tilt (canted angle) to add tension and dynamism as the lasers deflect incoming threats.
Narration: Intense and protective. "Passive defense is a risk you can't afford. Activate the grid. Neutralize the threat before it strikes."
Psychological Impact & KPI Focus
Niche Psychology: Appeals to the "Warrior" aspect of the security persona. When competitors pitch "compliance" (boring), this style pitches "defense" (exciting). It positions the platform as a weapon against bad actors, satisfying the desire for robust, high-tech protection.
Operational Impact: Visualizes Intrusion Prevention Systems (IPS). The lasers represent active rules blocking specific exploit attempts, distinguishing the platform from passive scanning tools.
Strategic Implementation & Trade-offs
Use Cases: Competitive comparison pages ("Us vs. Them"), feature highlights for active blocking modules, and trade show attract loops.
Duration: 15–20 seconds.
Trade-offs: Aggressive Tone. It is dark and intense. Use sparingly; too much can feel like "Fear, Uncertainty, and Doubt" (FUD) marketing if not balanced with positive outcomes.
Companies using similar video content -
HashiCorp – Terraform – Defines infrastructure using declarative configuration language.
Checkov – Checkov – Scans IaC templates for security and compliance issues pre-deployment.
18. Isometric 3D Workflow
BOFU | Sales Cycle Acceleration
The Visual & Narrative Approach
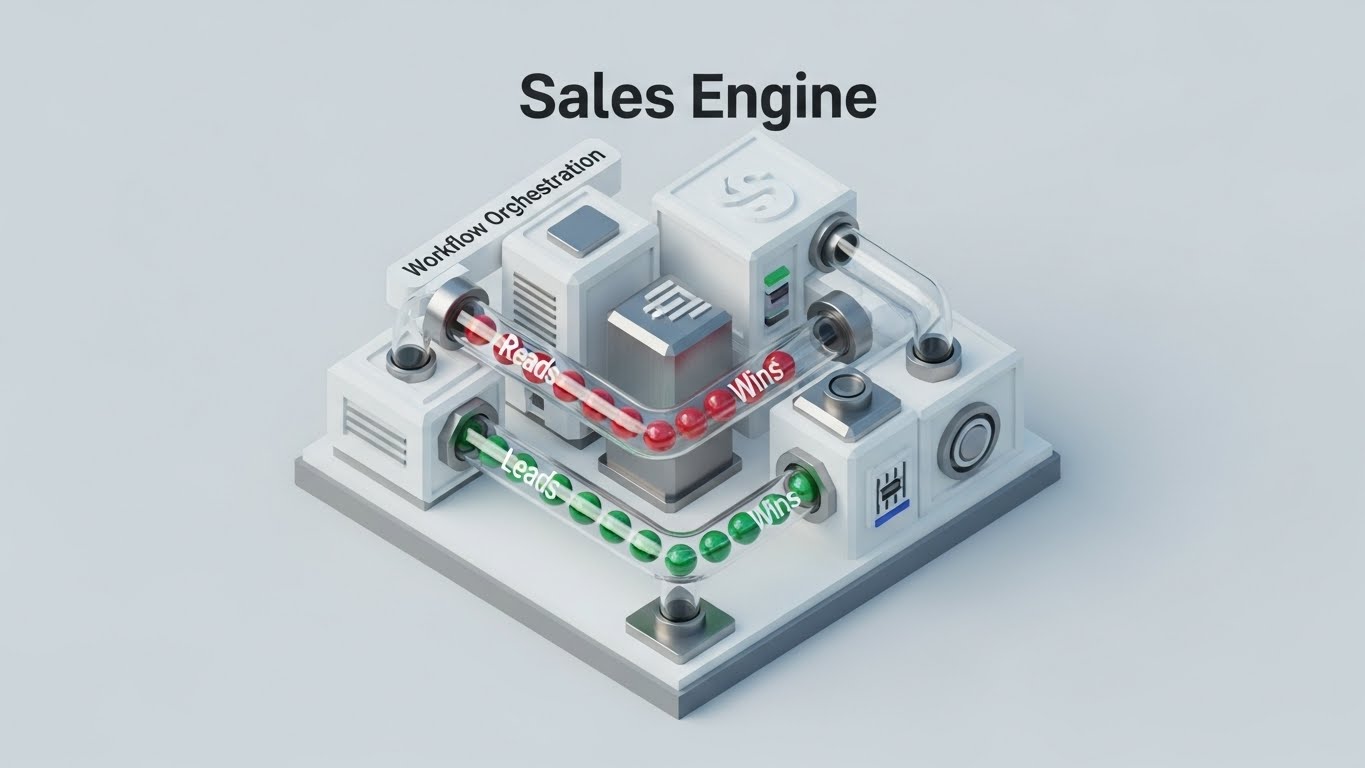
Scenario: An isometric 3D animation of a pristine white machine engine, representing the "Sales Engine." Red spheres labeled "Leads" enter the system through clear tubes. Inside the machine (representing the Security Platform's automated compliance engine), they are processed efficiently. They emerge on the other side as Green spheres labeled "Wins," dropping into a bin marked with a Dollar Sign. This visualizes Security as a Sales Enablement tool.
Narration: Business-focused and rhythmic. "Don't let security questionnaires slow you down. Automate compliance. Accelerate the deal. Turn leads into wins."
Psychological Impact & KPI Focus
Niche Psychology: Reverses the narrative that "Security is a blocker." Sales teams often view security reviews as a hurdle. This visual reframes the platform as a Sales Accelerator, helping the CISO sell the value of security to the CRO (Chief Revenue Officer).
Operational Impact: Visualizes Sales Cycle Acceleration. By automating the compliance posture (SOC2, ISO), the organization can pass vendor security reviews instantly, removing friction from their own sales process.
Strategic Implementation & Trade-offs
Use Cases: Conversations with the Board, content for the Sales Enablement team, or "ROI of Security" calculators.
Duration: 30–45 seconds.
Trade-offs: Concept Shift. It requires the audience to pivot from thinking about "hackers" to thinking about "revenue," which is a sophisticated B2B argument.
Companies using similar video content -
IBM – Security QRadar SOAR – Automates repetitive tasks to reduce response times.
Torq – HyperSOC – Empowers lean security teams with extensive SecOps automation.
19. Abstract 3D AI Visualization
BOFU | Objection Handling
The Visual & Narrative Approach
Scenario: A macro shot of a network of spherical nodes in Iridescent Pearl and Chrome. The central node pulses with light and sends a data signal along a Soft Pink connector line to neighboring nodes, which light up in response. This abstractly visualizes the "Ecosystem Integration"—the platform (central node) sharing intelligence with firewalls, ticket systems, and chat tools (neighbor nodes).
Narration: Sophisticated and connective. "Intelligence shouldn't be siloed. Create a nervous system for your security, where every part knows what the center knows."
Psychological Impact & KPI Focus
Niche Psychology: Overcomes the objection: "Just another tool to manage." By visualizing the platform as the connector or brain that energizes the existing stack, it frames the purchase as an Optimization of current investments, not just a new cost.
Operational Impact: Visualizes API Integration & Orchestration. The flow of light represents the automated sharing of threat data, reducing the manual "swivel-chair" work of analysts moving between tools.
Strategic Implementation & Trade-offs
Use Cases: Integration pages, "Ecosystem" brochures, and objection-handling videos addressing "tool sprawl."
Duration: 15–30 seconds.
Trade-offs: Abstract. It assumes the viewer understands the value of integration. It requires voiceover to ground the visual in reality.
Companies using similar video content -
Fortinet – FortiSOAR – Integrated SOAR solution within the Fortinet Security Fabric.
Palo Alto Networks – Cortex XDR – AI-driven analytics for faster threat identification.
20. Aspirational Stock Montage
BOFU | The Economic Buyer

The Visual & Narrative Approach
Scenario: The final closing argument. A cinematic shot of a CISO or CEO standing in a glass-walled office, looking out at a city skyline at dawn. The lighting is a cinematic sun flare creating a silhouette effect against a "Corporate Blue" sky. The expression is one of calm resolve and vision. The chaos of the earlier "alert fatigue" visuals is gone, replaced by stillness and clarity.
Narration: Inspirational and final. "Move from firefighting to leading. Build a legacy of resilience. This is security, elevated."
Psychological Impact & KPI Focus
Niche Psychology: Appeals to Self-Actualization. Every security leader wants to stop being the "fixer" and start being the "strategist." This style sells the feeling of having solved the problem. It targets the Economic Buyer (CFO/CEO) by projecting stability.
Operational Impact: Visualizes Strategic Resilience. It moves beyond metrics (MTTR) to the ultimate goal: Business Continuity and brand reputation.
Strategic Implementation & Trade-offs
Use Cases: The final video on the "About Us" page, the closing seconds of a demo video, or Investor Relations content.
Duration: 5–10 seconds.
Trade-offs: Emotional vs. Functional. This style sells the dream, not the feature. It is powerful for closing but useless for explaining how it works. It must be earned by the previous technical explanations.
Companies using similar video content -
Delve – Automated Compliance – AI agents eliminate compliance busywork.
Comp AI – Automated Compliance Software – Reduces audit prep time with automated evidence collection.
21. Clean UI Workflow (Light Mode)
Onboarding | Self-Serve Onboarding
The Visual & Narrative Approach
Scenario: A pristine, straight-on view of a floating interface panel in Lavender and Soft White. The design is airy and uncluttered, adhering to "Light Mode" aesthetics which signal approachability. We see a "Getting Started" checklist. As the narrative proceeds, satisfying, bright green checkmarks animate sequentially—click, pop, click, pop—indicating rapid progress. Soft drop shadows lift the UI elements off the Soft Grey background, giving a sense of lightness.
Narration: Encouraging and clear. "Setup shouldn't be a security risk in itself. Connect. Configure. Complete. In minutes, not months."
Psychological Impact & KPI Focus
Niche Psychology: Addresses the "Implementation Dread" common in enterprise software. CISOs fear buying "shelfware" that takes months to configure. This style visually proves that the barrier to entry is low.
Operational Impact: Visualizes Time-to-Value (TTV). By showing the speed of the "Setup Complete" state, it reassures the buyer that they will see ROI almost immediately after purchase.
Strategic Implementation & Trade-offs
Use Cases: Welcome emails, the first screen inside the app, or "Quick Start" video guides.
Duration: 15–30 seconds.
Trade-offs: Simplicity Masking. It hides the backend complexity. Ensure the "Easy" visual doesn't overpromise if the actual API integration is heavy.
Companies using similar video content -
Snyk – AI Security Platform – Integrates AI-powered workflows for development and security.
Anomali – The Anomali Platform – Modernizes security operations with analytics, intelligence, automation, and AI.
22. 2D Animation & UI Composition
Onboarding | Accelerating Time-to-Value

The Visual & Narrative Approach
Scenario: A dynamic interaction between a stylized 2D character (flat vector, Vibrant Orange and Teal) and the software interface. The character, representing a SecOps analyst, gestures toward a floating UI window that displays a "Vulnerability Patched" notification. The character high-fives the window or gives a thumbs-up, and the window glows in response. The background is abstract geometric shapes, keeping the focus on the relationship between user and tool.
Narration: Enthusiastic and human. "That feeling when the critical alert goes silent. Experience the win of a secure perimeter."
Psychological Impact & KPI Focus
Niche Psychology: Security is often thankless work. This style utilizes Gamification Psychology, visually rewarding the user for performing a task. It validates the analyst's effort, creating a positive emotional association with the tool.
Operational Impact: Visualizes User Adoption. By making the interaction feel "fun" and "rewarding," it encourages daily logins and proactive remediation habits.
Strategic Implementation & Trade-offs
Use Cases: "Congratulations" screens after a major patch cycle, or case study videos highlighting user satisfaction.
Duration: 10–15 seconds.
Trade-offs: Tone Management. Must not be too "cartoony" for a serious security product. The UI elements within the animation must remain accurate.
Companies using similar video content -
CrowdStrike – Falcon – Protects against advanced threats with cloud-native architecture.
SentinelOne – Singularity XDR – Simplifies modern cybersecurity through a centralized platform.
23. 2D Graphics Over Live Action
Onboarding | Reducing Implementation Friction

The Visual & Narrative Approach
Scenario: A live-action photo of a diverse team (Devs and Ops) collaborating around a meeting table. They look engaged and happy. Superimposed above their heads are floating 2D vector icons—Gears, Speech Bubbles, and Connectors in abstract geometric colors. The graphics animate to show a flow of information moving seamlessly between the "Developer" side and the "Security" side, bridging the gap.
Narration: Collaborative and unifying. "Security isn't a blocker; it's the bridge. Get Dev and Ops speaking the same language."
Psychological Impact & KPI Focus
Niche Psychology: Targets the "Cultural Divide" between DevOps (speed) and SecOps (safety). This style visualizes DevSecOps culture—showing real humans working together, aided by the software's translation layer.
Operational Impact: Visualizes Cross-Functional Collaboration. It demonstrates that the platform reduces friction in the remediation workflow, leading to faster ticket resolution.
Strategic Implementation & Trade-offs
Use Cases: "Culture" pages, onboarding training for mixed teams, and internal stakeholder presentations.
Duration: 30–60 seconds.
Trade-offs: Stock Photo Quality. Requires high-end, authentic stock photography to avoid the "cheesy corporate meeting" vibe.
Companies using similar video content -
Tines – No-Code Automation Engine – Enables teams to automate menial repetitive tasks.
n8n – Automation Software – Automates SecOps workflows with customizable tools.
24. Macro UI Micro-Interactions
Onboarding | Trial/Freemium User Activation

The Visual & Narrative Approach
Scenario: An extreme close-up (macro) shot of a specific UI button glowing Electric Blue against a Dark Grey surface. The text on the button reads "One-Click Remediation." A mouse cursor hovers, anticipating the click. The depth of field is shallow, blurring the edges and focusing all attention on the action. The cursor clicks, and the button pulses with a satisfying ripple effect, changing to "Resolved."
Narration: Short, punchy, and tactile. "See it. Click it. Fixed. The power of precision at your fingertips."
Psychological Impact & KPI Focus
Niche Psychology: Appeals to the desire for Control and Immediacy. In a complex world of command-line interfaces, a simple, powerful button is deeply satisfying. It promises low effort for high reward.
Operational Impact: Visualizes Ease of Use. It provides the "proof" for the marketing claim of "automated remediation," showing exactly how simple the execution is.
Strategic Implementation & Trade-offs
Use Cases: Social media ads (Instagram/LinkedIn), feature tooltips within the app, and "New Feature" announcement snippets.
Duration: 5–10 seconds (Looping).
Trade-offs: Context Loss. It shows the action but not the result. Best used in conjunction with broader context videos.
Companies using similar video content -
KnowBe4 – PhishER Plus – Helps detect phishing attacks and initiates incident response faster.
OpenVAS – Open Vulnerability Assessment System – Provides a robust suite of vulnerability checks.
25. 2D Character-Driven Story
Retention | Reducing Support Overhead
The Visual & Narrative Approach
Scenario: A flat 2D vector illustration in the "Corporate Memphis" style (clean lines, exaggerated limbs, flat colors). A security analyst sits relaxed at a desk with feet up, sipping coffee from a Red mug. Beside them, a stylized server rack glows with a "Working" light, handling the load automatically. The palette uses Muted Earth Tones to suggest calmness, contrasting with the high-stress red of typical security alerts.
Narration: Empathetic and relaxed. "Let the system handle the night shift. You handle the strategy. Reclaim your weekends."
Psychological Impact & KPI Focus
Niche Psychology: Directly targets Burnout and Alert Fatigue. It doesn't sell "better security"; it sells "better quality of life." It positions the platform as a partner that gives time back to the human operator.
Operational Impact: Visualizes Support Ticket Reduction. By showing the system self-remediating (the glowing server), it implies fewer manual interventions and less need for support calls.
Strategic Implementation & Trade-offs
Use Cases: Customer success newsletters, "Help Center" waiting screens, and retention campaigns.
Duration: 15–20 seconds.
Trade-offs: Seriousness. This style is lighthearted. Avoid using it for "Critical Breach" communications; keep it for "Efficiency" topics.
Companies using similar video content -
Snyk – Developer Security Platform – Accelerates secure, AI-driven development.
Defect Dojo – Defect Dojo – Open-source vulnerability management for DevSecOps.
26. Low-Poly 3D Modeling
Retention | Reducing Churn

The Visual & Narrative Approach
Scenario: A playful yet structural Low-Poly 3D scene. A blue plastic shopping cart (representing the "Inventory" or "Project") sits in a blue void. Geometric shapes (cubes, pyramids, spheres) in Red, Yellow, and Green fall from above, filling the cart. Each shape represents a different asset type (Server, Cloud Instance, Laptop) being "collected" and accounted for. The shapes settle perfectly, emphasizing capacity and organization.
Narration: Constructive and steady. "You can't secure what you can't see. Gather your assets. Organize your inventory. Build a complete picture."
Psychological Impact & KPI Focus
Niche Psychology: Addresses the anxiety of "Shadow IT" and unknown assets. The visual of "collecting" everything into one place (the cart) satisfies the CISO's need for a comprehensive Asset Inventory.
Operational Impact: Visualizes Stickiness. As the cart fills up, it represents the growing value of the platform. The more assets managed, the harder it is to churn.
Strategic Implementation & Trade-offs
Use Cases: "Year in Review" videos ("Look how many assets you secured!"), onboarding steps for asset discovery, or pricing pages based on "per-asset" models.
Duration: 20–30 seconds.
Trade-offs: Metaphorical. The shopping cart is a strong metaphor for "Commerce," so ensure the context emphasizes "Inventory/Collection" rather than "Buying."
Companies using similar video content -
Symantec – Advanced Threat Protection – One-click containment and remediation capability.
Xcitium – EDR – Blocks attacks, malware, and malware-free threats.
27. Holographic UI over 3D Render
Retention | Proactive Support

The Visual & Narrative Approach
Scenario: A first-person POV shot. A hand holds a tablet in a blurred office setting. Projecting upward from the screen is a 3D Hologram in luminous Blue and Magenta. The hologram displays abstract nodes and data streams representing "Future-Proof" updates or AI predictions. It feels like Iron Man’s technology—advanced, predictive, and cutting-edge.
Narration: Futuristic and visionary. "The threat landscape changes daily. Your platform should too. See what’s coming before it lands."
Psychological Impact & KPI Focus
Niche Psychology: Targets the FOMO (Fear Of Missing Out) on innovation. Security leaders want to feel they are using "Next-Gen" tech. This style assures them that their current subscription includes cutting-edge capabilities.
Operational Impact: Visualizes Predictive Maintenance/Security. It suggests the platform is proactive, identifying issues via AI (the hologram) before they become incidents.
Strategic Implementation & Trade-offs
Use Cases: Product update emails, "What's New" webinars, and renewal presentations to justify price increases.
Duration: 15–20 seconds.
Trade-offs: Hype Check. The visual promises sci-fi capabilities. Ensure the actual feature release (e.g., AI prediction) justifies the futuristic aesthetic.
Companies using similar video content -
Trellix – ePolicy Orchestrator (ePO) – Reshapes cybersecurity landscape with machine learning and automation.
Blumira – Automated Detection and Response – SIEM plus XDR platform makes advanced detection easy.
28. Dark Mode UI Showcase
Expansion | Driving Deep Feature Adoption

The Visual & Narrative Approach
Scenario: A close-up of a curved screen displaying the platform's "Dark Mode" interface. Cascading lines of code and log data scroll rapidly. As they scroll, specific lines transition from an alert Red to a secure Green. The background is Midnight Blue with Bioluminescent Blue UI accents. The aesthetic is "The Matrix" meets "Enterprise Dashboard."
Narration: Technical and intense. "Dive deep. Scan the code, not just the surface. Find the needle in the haystack."
Psychological Impact & KPI Focus
Niche Psychology: Appeals to the Deep Practitioner (Tier 3 Analysts/Architects). They trust "Dark Mode" and raw data. This style signals that the tool is not just a pretty dashboard for management but a serious tool for code-level remediation.
Operational Impact: Visualizes Feature Depth. It highlights advanced capabilities like "Infrastructure as Code Scanning" or "Log Analysis," encouraging customers to upgrade to higher tiers.
Strategic Implementation & Trade-offs
Use Cases: Advanced technical tutorials, documentation headers, and "Pro Tier" feature pages.
Duration: 30–60 seconds.
Trade-offs: Readability. Moving code can be hard to read. Use freeze-frames to highlight specific remediation lines.
Companies using similar video content -
Nodeware – Nodeware – Continuous vulnerability management with real-time visibility into network assets.
Armis – Centrix – Protects the entire attack surface and manages cyber risk exposure.
29. 3D Parallax UI Presentation
Expansion | Driving Upsell/Cross-sell

The Visual & Narrative Approach
Scenario: A 3D composition where the UI is deconstructed into floating layers (glass sheets). The bottom layers are Grey (Basic features). The middle layers are Silver. The top layer, representing "Premium Features" or "Add-on Modules," glows in Gold and Platinum, physically elevated above the rest. The camera pans sideways to emphasize the depth and the "stacking" of value.
Narration: Value-driven. "Elevate your posture. Unlock the gold standard of remediation with the Enterprise Module."
Psychological Impact & KPI Focus
Niche Psychology: Visualizes Value Stratification. It subtly makes the "Basic" tier look incomplete or flat, while the "Premium" tier looks aspirational and elevated. It triggers the desire to "complete the stack."
Operational Impact: Visualizes Upsell Value. It clearly distinguishes between what the customer has (flat layers) and what they could have (elevated gold layer), aiding the Customer Success Manager in upgrade conversations.
Strategic Implementation & Trade-offs
Use Cases: "Upgrade" landing pages, QBR (Quarterly Business Review) decks, and pricing pages.
Duration: 15–20 seconds.
Trade-offs: Subtlety. It must not look like a "paywall." It should look like an "enhancement."
Companies using similar video content -
Darktrace – Enterprise Immune System – Leverages AI to autonomously detect and respond to threats.
Google – SecOps – Integrates Gemini, a gen-AI model providing natural language interaction.
30. Generative AI Realistic Character
Expansion | Driving Referrals & Advocacy

The Visual & Narrative Approach
Scenario: A photorealistic video generated by AI. A professional male speaker in a suit, shot with a shallow depth of field (cinematic bokeh). He speaks directly to the camera with a genuine, enthusiastic expression. The lighting is high-end studio quality. The background is a blurred, modern high-tech office. He is delivering a "testimonial" or a "peer recommendation" script.
Narration: Sincere and direct. "We didn't just fix vulnerabilities; we changed our culture. If you're on the fence, trust me—this is the shift you need."
Psychological Impact & KPI Focus
Niche Psychology: Leverages Social Proof. In B2B Security, decision-makers trust their peers more than vendors. Using a hyper-realistic avatar to deliver synthesized "Case Study" highlights creates a personal connection without the logistical cost of filming real clients.
Operational Impact: Visualizes Advocacy. It humanizes the success story, making the ROI feel tangible and personal, which drives referrals.
Strategic Implementation & Trade-offs
Use Cases: LinkedIn social proof posts, "Customer Stories" page intros, and community newsletters.
Duration: 30–60 seconds.
Trade-offs: Uncanny Valley. The AI generation must be top-tier (e.g., HeyGen/Synthesia quality). If it looks robotic, trust is instantly destroyed.
Strategic Knowledge Base: The Visual Operations Doctrine
To truly bridge the "Remediation Gap," we must move beyond treating video as "marketing content." In the context of a Security SaaS platform, visualization is an Operational Tool. It is the language used to translate the abstract terror of a vulnerability into the concrete action of a patch.
The following three frameworks provide the strategic scaffolding to implement these 30 visual styles effectively. They are designed to align your visual strategy with the specific pressures of the Cybersecurity industry.
Strategic Alignment & Visual Architecture
The "Pre-Production" Strategy. Why we visualize and for whom.
- The Cognitive Load Audit: Before creating a single pixel, audit your current training materials. If a PDF takes 20 minutes to read, replace it with a Style 2 (Isometric) video that takes 45 seconds. Measure the time saved per analyst.
- Role-Based Visual Mapping: Do not use the same visuals for the Analyst as the Board. Use Style 28 (Dark Mode) for the analyst to prove technical depth, but use Style 7 (Glassmorphic Charts) for the Board to prove ROI.
- The "Glanceability" Standard: In a SOC (Security Operations Center), data must be readable in milliseconds. Your product videos should mimic this. Avoid clutter; prioritize the "Signal" (the threat) over the "Noise" (the background), as seen in Style 6 (Abstract Motion).
- Brand Voice Consistency: Your marketing videos (external) and your product UI (internal) must speak the same visual language. If marketing is "Cyberpunk Neon" but the product is "Flat Grey," you create a Trust Gap.
- The Advids Strategic Audit: Partner with Advids to define this "Visual Operating System" before production begins. We align your visual hierarchy with your specific buyer personas (e.g., the "Pragmatic Guardian").
- Standardization vs. Customization: Use standardized "Stock + UI" (Style 13) for generic top-of-funnel content to save budget. Reserve bespoke 3D renders (Style 9) for your core differentiators (e.g., your proprietary AI engine).
- The Cross-Departmental Bridge: Use visuals to unify terminology. If Sales says "Risk," Ops says "CVE," and Board says "Loss," use Style 16 (Split Screen) to visually link these terms into a single narrative.
- Legacy System Integration: Visualizing the connection between old on-premise hardware and new SaaS interfaces is critical. Use Style 15 (Wireframe to Reality) to show how your platform wraps around and modernizes legacy tech.
- Accessibility in Operations: Security is global. Ensure your motion graphics rely on visual cues (color changes, shape morphs) rather than just text, ensuring the message lands across language barriers (Style 5).
- The Mobile-First Mandate: CISOs approve POs on their phones. Ensure all styles, especially Style 13 (Lifestyle) and Style 24 (Macro UI), are legible on a vertical mobile screen.
Operational Adoption & Implementation
The "Deployment" Phase. How to embed visuals into the workflow.
- Overcoming "Big Brother" Anxiety: Automated remediation can feel like a loss of control. Use Style 23 (Mixed Media) to show humans collaborating with the AI, not being replaced by it.
- The Micro-Learning Shift: Stop forcing analysts to watch hour-long webinars. Embed Style 21 (Clean UI) loops directly into the Jira ticket or the software tooltip for "Just-in-Time" learning.
- Just-in-Time Support: Embed specific visual styles into the Help Center. A user stuck on configuration should see Style 2 (Isometric) to understand the architecture, then Style 24 (Macro UI) to see the button to click.
- Gamification of Training: Use Style 22 (2D Animation) in your internal "Security Champions" training. Visual rewards (animations of fixing bugs) drive higher engagement than text checklists.
- Reducing Support Ticket Volume: There is a direct correlation between proactive visual guides and reduced call center load. If users can see the fix (Style 24), they won't call support.
- Remote Onboarding: Leverage Style 8 (Rapid UI) to train distributed teams. You cannot rely on "over the shoulder" training in a remote world; the video must be the mentor.
- Standard Operating Procedures (SOPs): Transform static text-based SOPs into visual process flows using Style 10 (Line Art). "Unravel" the complex process into a simple straight line.
- Feedback Loops: Use interactive video elements. If a user drops off during a Style 28 (Code Scan) video, it may be too technical. Use this data to refine the complexity.
- Scalable Localization: When expanding to new regions (EMEA/APAC), use Style 1 (Abstract) and Style 4 (Kinetic Typo). These styles are easily localized by swapping text layers without reshooting footage.
- Leadership Communication: When the CISO presents to the Board, provide them with Style 20 (Aspirational Stock). Help them sell the vision of security, not just the tactics.
Measuring Impact & Future-Proofing
The "ROI" Phase. Measuring success and looking ahead.
- Beyond "Views": Don't measure video views. Measure "Time-to-Competency." How much faster does a new analyst patch a server after watching the Style 8 video vs. reading the manual?
- The "Idle Time" Metric: Correlate better visualization with reduced software navigation time. If the UI is intuitive (as shown in Style 21), "Idle Time" decreases.
- Compliance Velocity: Measure how fast new regulations (e.g., DORA, SEC rules) are understood by the team when explained via Style 2 (Isometric) vs. a memo.
- Retention and Churn: High-quality UX visualization (Style 22) increases perceived value. Customers who "feel" the success of the tool are less likely to churn.
- The AI Visual Frontier: Prepare for generative video. Start building a library of "Clean UI" assets (Style 21) that can be fed into AI tools to generate personalized onboarding videos for every client.
- Scalability of Assets: Build a library, not a landfill. Style 26 (Low Poly) allows you to add new "blocks" (features) to the existing video without re-rendering the whole scene.
- The Advids Partnership: Visual strategy is not a one-off project; it is an operational layer. Advids acts as your long-term partner, ensuring your visual library evolves as your platform scales from V1 to V2.
- Benchmarking Success: "Good enough" visuals are a competitive risk. If your competitor uses Style 9 (3D Render) and you use static screenshots, you look like the legacy option.
- The ROI of Safety: Quantify the reduction in "Breach Probability" and link it to the training investment. "We spent $X on visual training and reduced phishing clicks by Y%."
- Final Call to Innovation: Treat video as Infrastructure, not content. It is the fiber-optic cable that carries understanding from your code to your customer's brain. Build it with the same rigor you build your software.
Companies using similar video content -
Elastic – Security – Open-source solution for threat hunting, SIEM, and endpoint security.
Trivy – Trivy – Best tool for teams that use containerized applications.

 /home/wwwroot/advids.co/design/index.php on line 425
/home/wwwroot/advids.co/design/index.php on line 425